漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0151052
漏洞标题:觅食账户体系控制不严导致(45W+用户信息泄露)
相关厂商:觅食
漏洞作者: 路人甲
提交时间:2015-11-04 17:51
修复时间:2015-12-19 19:54
公开时间:2015-12-19 19:54
漏洞类型:账户体系控制不严
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-04: 细节已通知厂商并且等待厂商处理中
2015-11-04: 厂商已经确认,细节仅向厂商公开
2015-11-14: 细节向核心白帽子及相关领域专家公开
2015-11-24: 细节向普通白帽子公开
2015-12-04: 细节向实习白帽子公开
2015-12-19: 细节向公众公开
简要描述:
RT
详细说明:
觅食APP,在应用宝17W下载量
API
#Base Path
MishiHost = http://test-api.mishi.cn/api
MishiH5Host = http://test-h5.mishi.cn
MishiFileHost = http://test-upload.mishi.cn
#Login Service
PostLoginAPIURI = ${MishiHost}/user/login
PostLogoutAPIURI = ${MishiHost}/user/logout
GetIsLoginUserAPIURI = ${MishiHost}/user/isLoginUser
PutUpdateUserAppStatusAPIURI = ${MishiHost}/user/appStatus
#UserSecurity Service
PutValidatePwdAPIURI = ${MishiHost}/user/validateLoginPwd
#UserIm Service
GetFindUserImByUserIdAPIURI = ${MishiHost}/userIm
PutModifyUserImPushEnableAPIURI = ${MishiHost}/userIm/pushEnable
#UserMgr Service
PutResetPasswordAPIURI = ${MishiHost}/user/password
PutUpdateUserBasicInfoAPIURI = ${MishiHost}/user/basicInfo
#Register Service
RegisterPath = ${MishiHost}/user/register
GetIsRegisterAPIURI = ${RegisterPath}/isRegister
PostSendSmsCaptchaAPIURI = ${RegisterPath}/sendSmsCaptcha
PostValidateSmsCaptchaAPIURI = ${RegisterPath}/validateSmsCaptcha
PostRegisterAPIURI = ${RegisterPath}
GetOldSendUserPhoneAuthForRegAPIURI = ${RegisterPath}/verificationCode/%s
PostNewSendUserPhoneAuthForRegAPIURI= ${RegisterPath}/verificationCode
GetValidatePhoneAuthForRegAPIURI = ${RegisterPath}/validatePhone
PostRegisterForH5APIURI = ${MishiH5Host}/user/register/h5
#UploadAttach Service
PostUploadAttachAPIURI = ${MishiFileHost}/upload/attach
#BuyerAddress Service
PostAddAddressAPIURI = ${MishiHost}/user/%s/address
GetBuyerAddressListByUserIdAPIURI = ${MishiHost}/user/%s/addresses
DeleteAddressAPIURI = ${MishiHost}/user/%s/address/%s
PutUpdateBuyerAddressAPIURI = ${MishiHost}/user/%s/address
GetBuyerAddressByAddressIdAPIURI = ${MishiHost}/user/address/%s
#Order Service
GetQueryOrdersAPIURI = ${MishiHost}/order/list
GetOrderListSettingAPIURI = ${MishiHost}/order/list/setting
#SearchIndex Service
GetSearchGoodsAndShopsAPIURI = ${MishiHost}/index/search
#Activity Service
GetVerifyActivityGoodsNumAPIURI = ${MishiHost}/activity/verify/%s
#Chef Service
GetShopMgrHomeByShopIdAPIURI = ${MishiHost}/shop/%s/mgrHome
#Stat Service
GetFindUserStatAPIURI = ${MishiHost}/stat/user
#Address Service
GetQueryAllRegionAPIURI = ${MishiHost}/address/region
证明
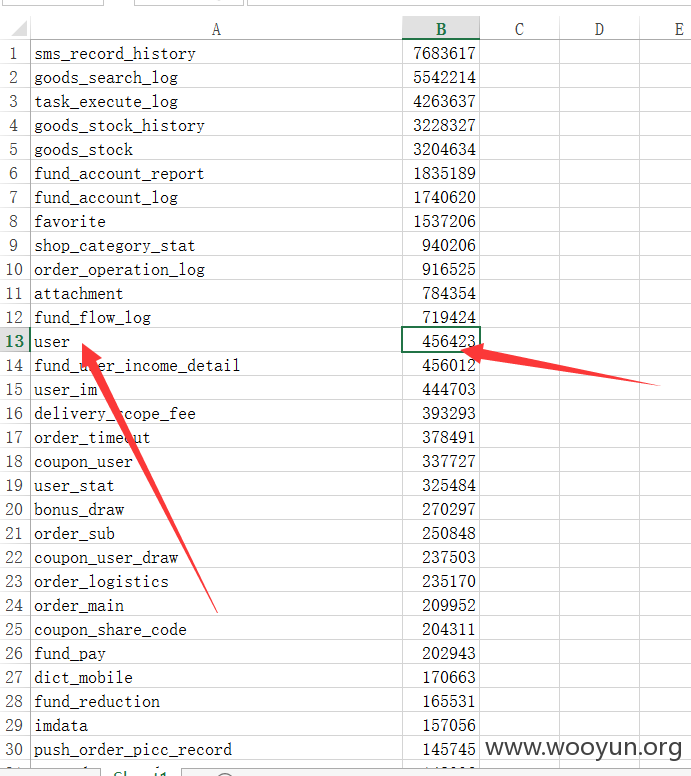
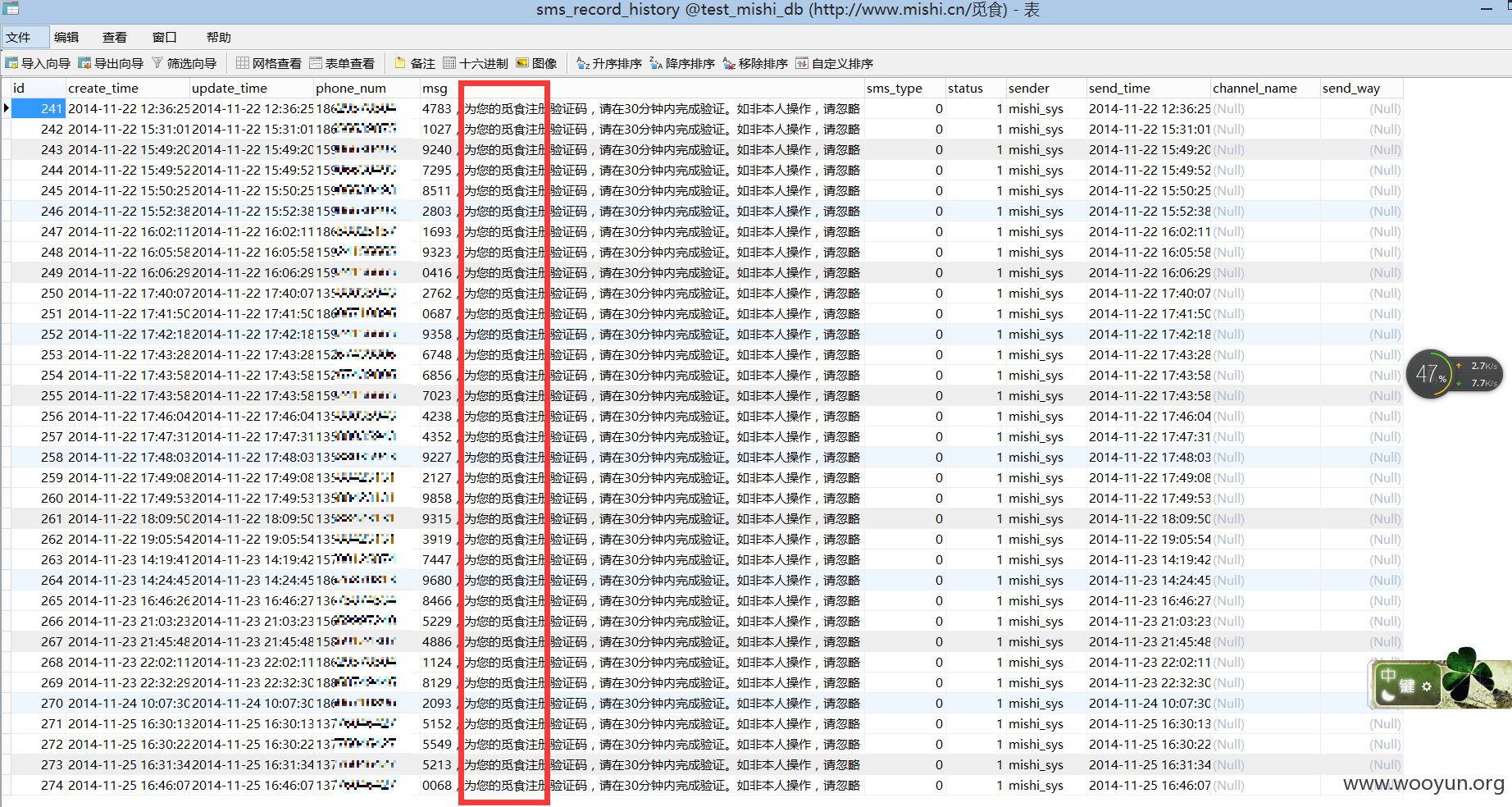
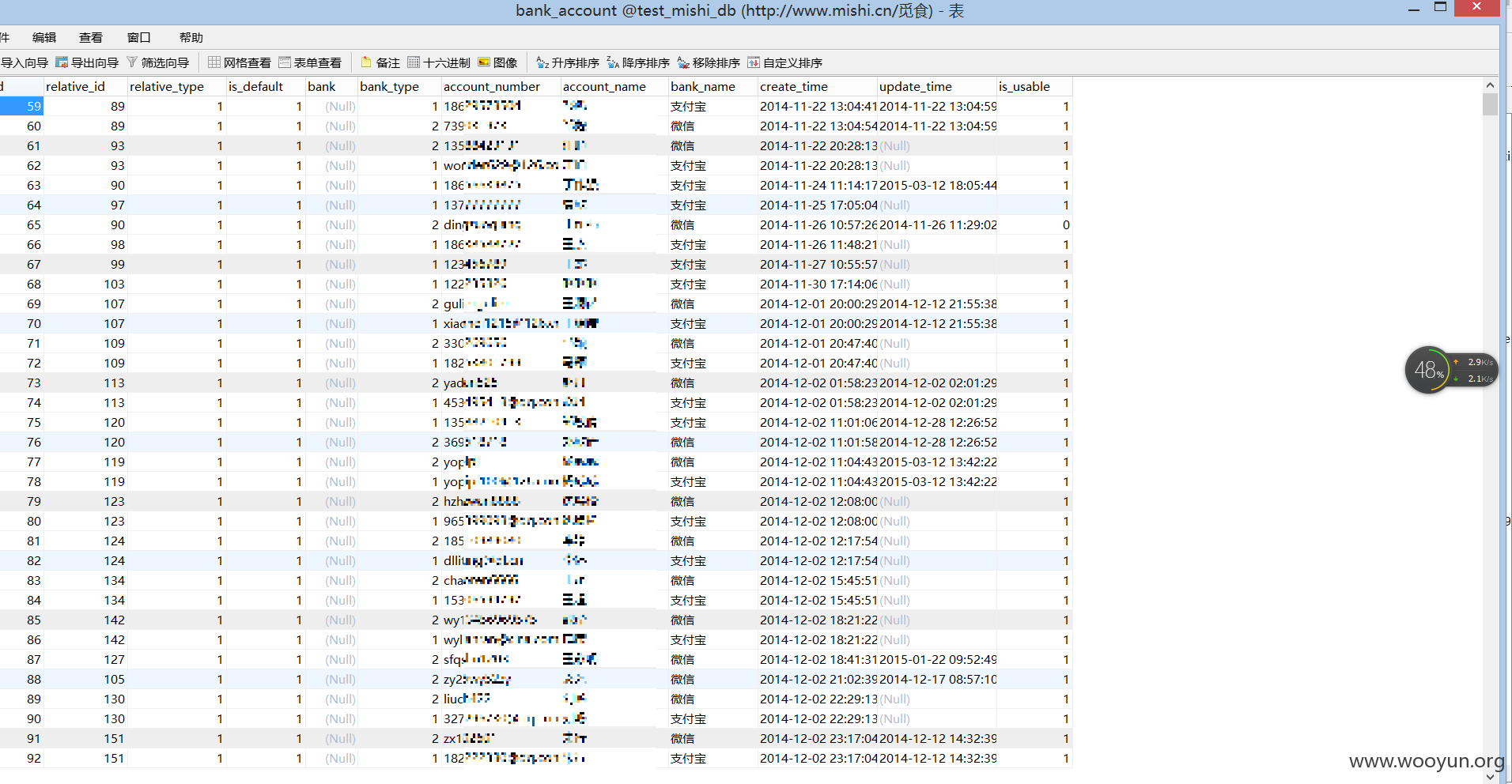
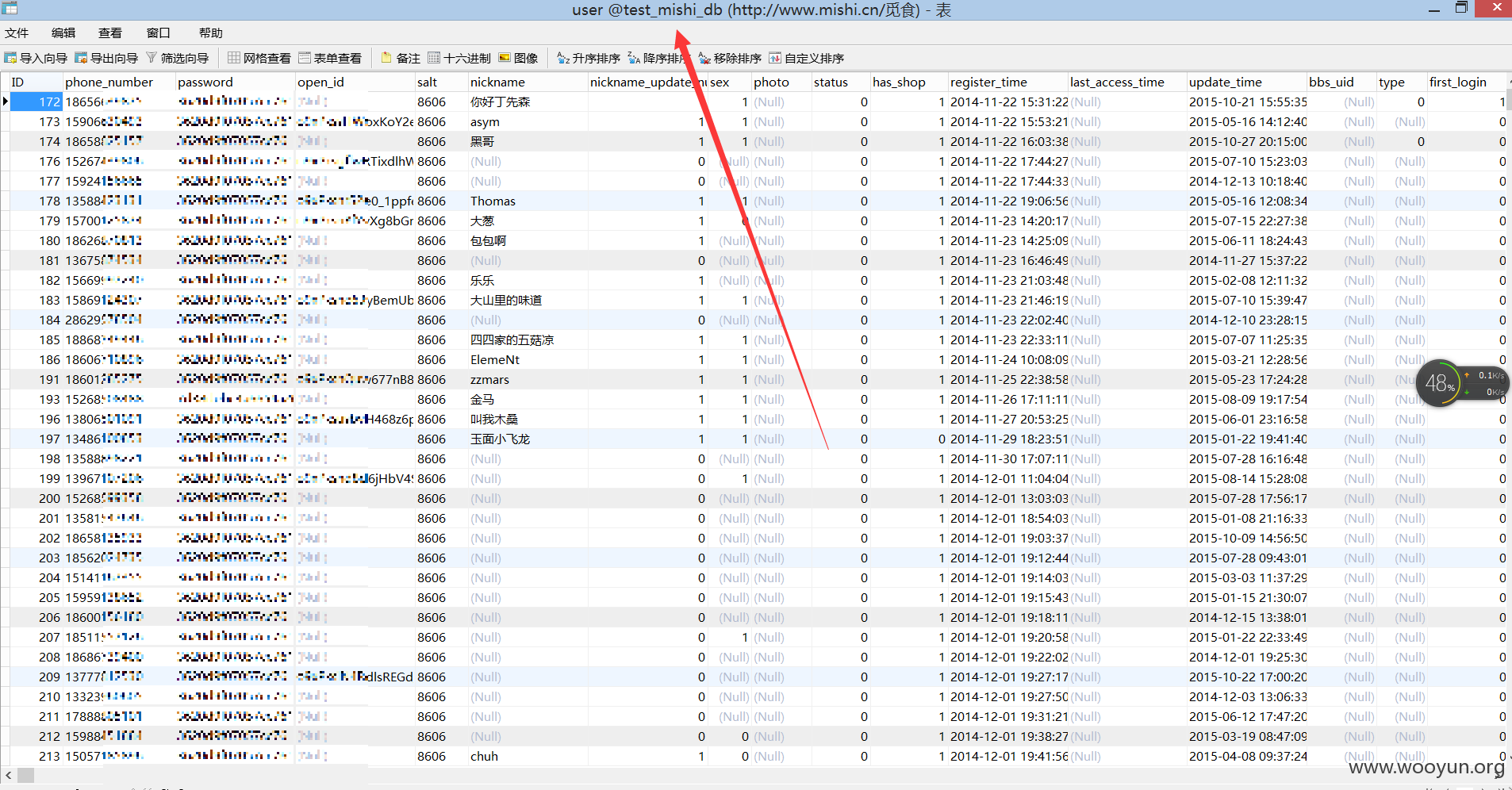
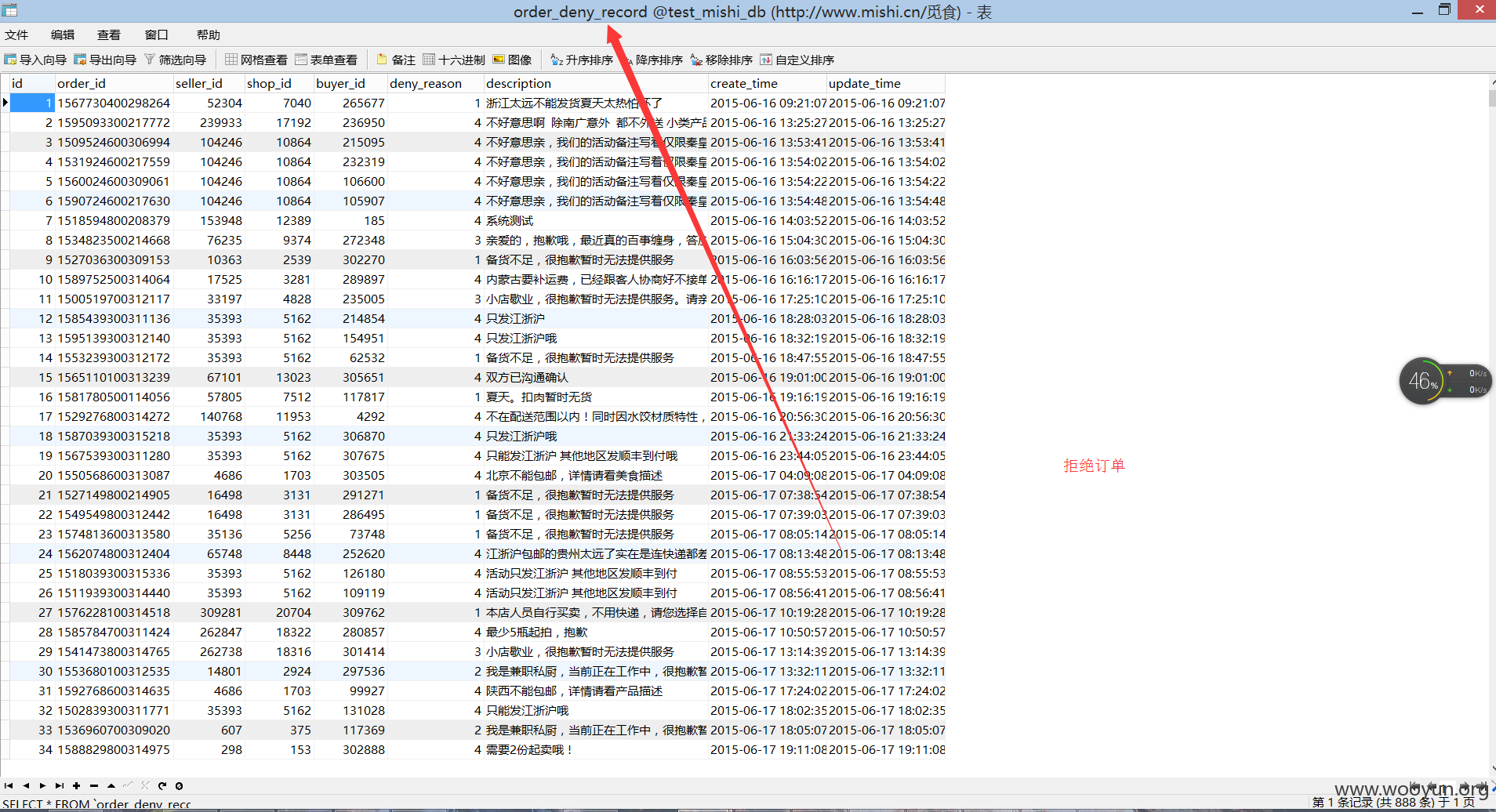
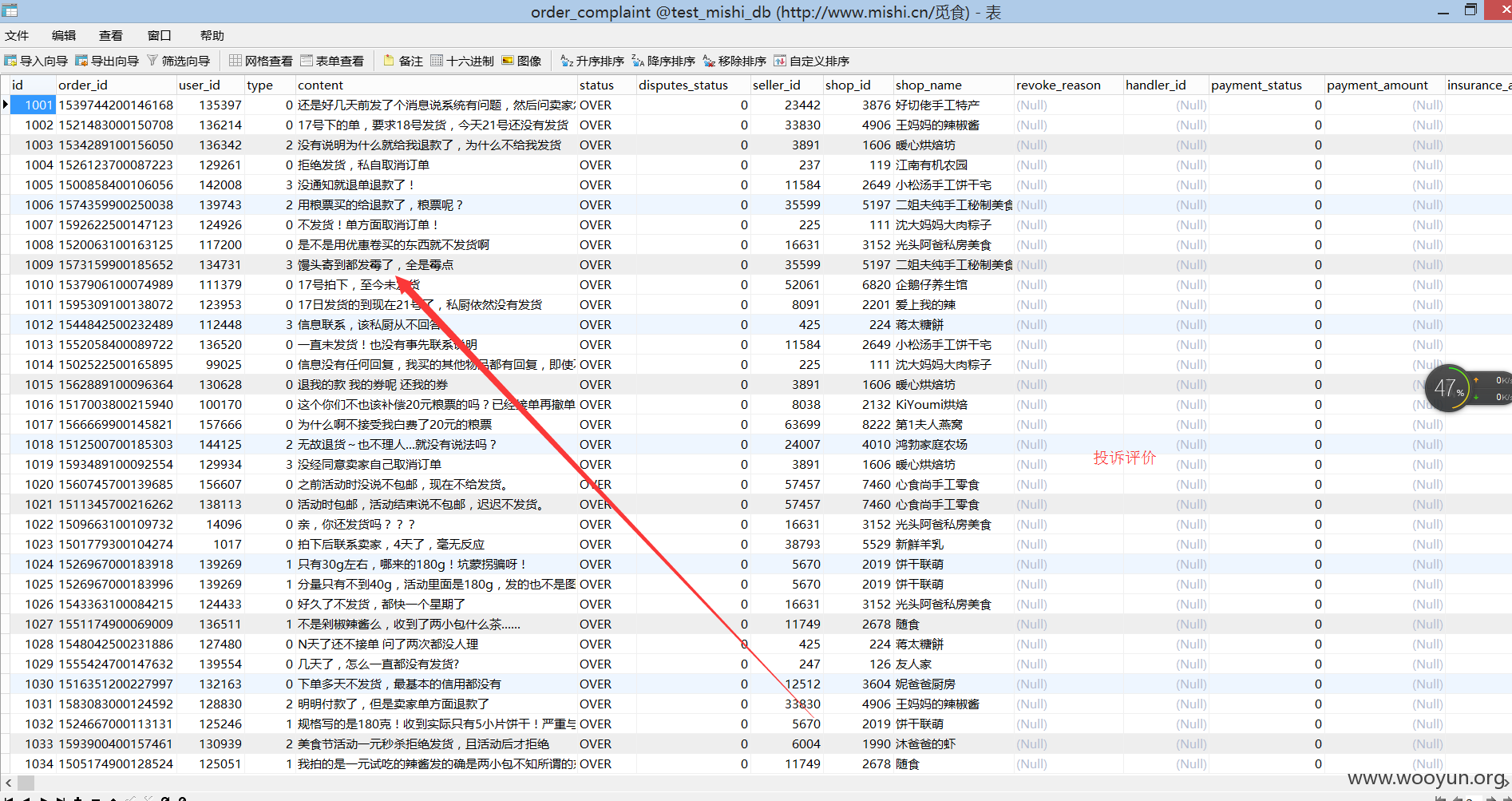
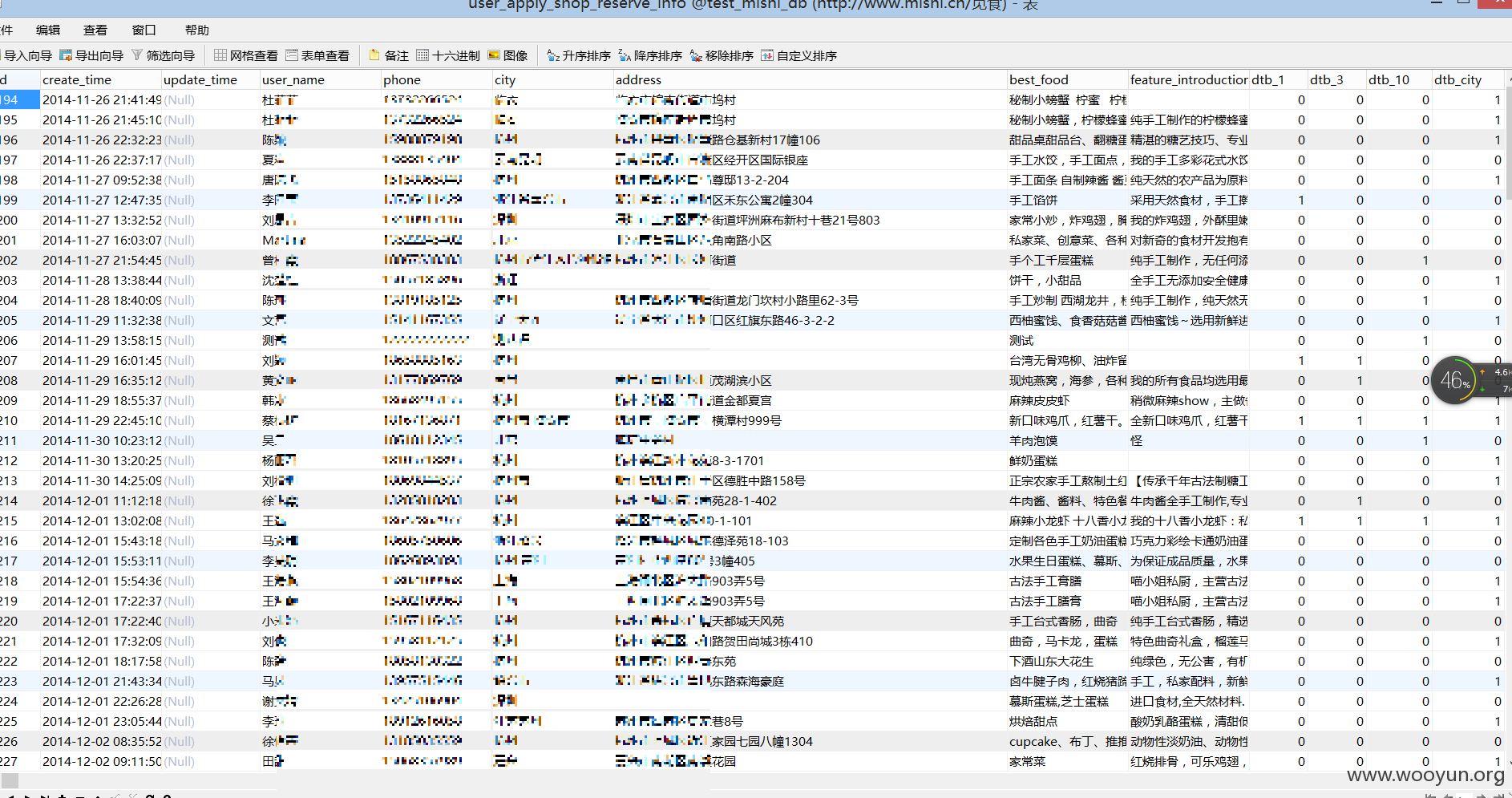
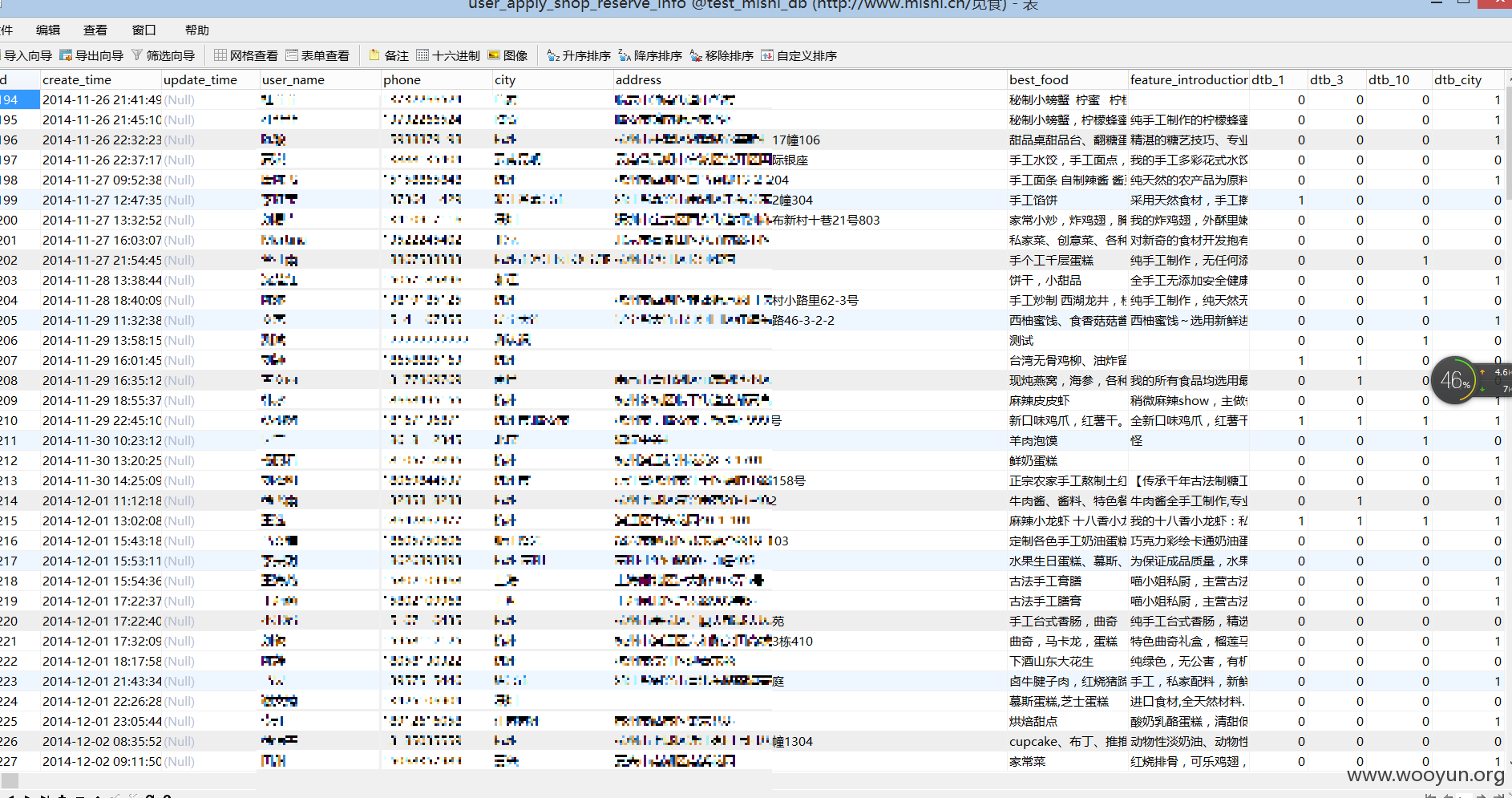
用户45W,还有商家门店
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-11-04 19:52
厂商回复:
谢谢帮助我们发现这个严重的泄露事件!请问@路人甲是否保存了数据库的备份?
最新状态:
2015-11-06:已解决