漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0138421
漏洞标题:北京市某县发改委存在SQL伪静态注入漏洞
相关厂商:北京市某县发改委
漏洞作者: 路人甲
提交时间:2015-09-04 10:30
修复时间:2015-10-22 08:28
公开时间:2015-10-22 08:28
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-04: 细节已通知厂商并且等待厂商处理中
2015-09-07: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-09-17: 细节向核心白帽子及相关领域专家公开
2015-09-27: 细节向普通白帽子公开
2015-10-07: 细节向实习白帽子公开
2015-10-22: 细节向公众公开
简要描述:
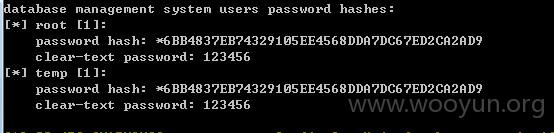
RT,root权限伪静态注入,root密码也是弱密钥……
政府网站就不深入了……
详细说明:
测试链接:
http://**.**.**.**/policy/display/9.do
Database: mysql
[23 tables]
+---------------------------------------+
| user |
| columns_priv |
| db |
| event |
| func |
| general_log |
| help_category |
| help_keyword |
| help_relation |
| help_topic |
| host |
| ndb_binlog_index |
| plugin |
| proc |
| procs_priv |
| servers |
| slow_log |
| tables_priv |
| time_zone |
| time_zone_leap_second |
| time_zone_name |
| time_zone_transition |
| time_zone_transition_type |
+---------------------------------------+
Database: fgwdb
[17 tables]
+---------------------------------------+
| authorities |
| deptintro |
| download |
| fggongwei |
| govsatisfaction |
| keshiset |
| ksnews |
| leader |
| leaderpost |
| link |
| magazine |
| notice |
| picnews |
| policy |
| users |
| websiteconfig |
| worknews |
+---------------------------------------+
Database: mei_wp
[11 tables]
+---------------------------------------+
| wp_commentmeta |
| wp_comments |
| wp_links |
| wp_options |
| wp_postmeta |
| wp_posts |
| wp_term_relationships |
| wp_term_taxonomy |
| wp_terms |
| wp_usermeta |
| wp_users |
+---------------------------------------+
Database: information_schema
[28 tables]
+---------------------------------------+
| CHARACTER_SETS |
| COLLATIONS |
| COLLATION_CHARACTER_SET_APPLICABILITY |
| COLUMNS |
| COLUMN_PRIVILEGES |
| ENGINES |
| EVENTS |
| FILES |
| GLOBAL_STATUS |
| GLOBAL_VARIABLES |
| KEY_COLUMN_USAGE |
| PARTITIONS |
| PLUGINS |
| PROCESSLIST |
| PROFILING |
| REFERENTIAL_CONSTRAINTS |
| ROUTINES |
| SCHEMATA |
| SCHEMA_PRIVILEGES |
| SESSION_STATUS |
| SESSION_VARIABLES |
| STATISTICS |
| TABLES |
| TABLE_CONSTRAINTS |
| TABLE_PRIVILEGES |
| TRIGGERS |
| USER_PRIVILEGES |
| VIEWS |
+---------------------------------------+
Database: feng_wp
[11 tables]
+---------------------------------------+
| wp_commentmeta |
| wp_comments |
| wp_links |
| wp_options |
| wp_postmeta |
| wp_posts |
| wp_term_relationships |
| wp_term_taxonomy |
| wp_terms |
| wp_usermeta |
| wp_users |
+---------------------------------------+
漏洞证明:
修复方案:
没跑管理员密码,不知道后台有没有洞?
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-09-07 08:26
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给北京分中心,由其后续协调网站管理单位处置。同时同步通报给北京市政府信息化主管部门.
最新状态:
暂无