漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0127282
漏洞标题:Suning某站点SQL注入漏洞(附验证脚本及脚本编写注意事项)
相关厂商:江苏苏宁易购电子商务有限公司
漏洞作者: Coody
提交时间:2015-07-17 06:51
修复时间:2015-08-31 09:00
公开时间:2015-08-31 09:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-17: 细节已通知厂商并且等待厂商处理中
2015-07-17: 厂商已经确认,细节仅向厂商公开
2015-07-27: 细节向核心白帽子及相关领域专家公开
2015-08-06: 细节向普通白帽子公开
2015-08-16: 细节向实习白帽子公开
2015-08-31: 细节向公众公开
简要描述:
1. 预祝{乌云峰会}圆满成功! 乌云:呱唧呱唧……
2. 编写python利用脚本时,不要使用url encode后的编码,因为 urllib.urlencode 方法替你做这件事情的.
详细说明:
漏洞站点:online.suning.com
测试代码:
漏洞成因:与服务端交互时,直接给参数赋值了sql语句,从而导致用户输入什么,服务端就会执行该sql语句。
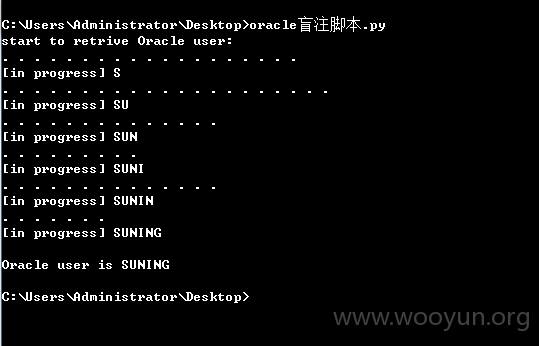
直接使用验证脚本跑注入即可。
当前用户名称为“SUNING”
漏洞证明:
利用脚本:
修复方案:
版权声明:转载请注明来源 Coody@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-07-17 09:00
厂商回复:
感谢提交,稍后送卡。
最新状态:
暂无