漏洞网站:ssvideo.chaoxing.com
网站需要登录才能访问,手工猜出来一个test/test
登录之后即可访问网站。
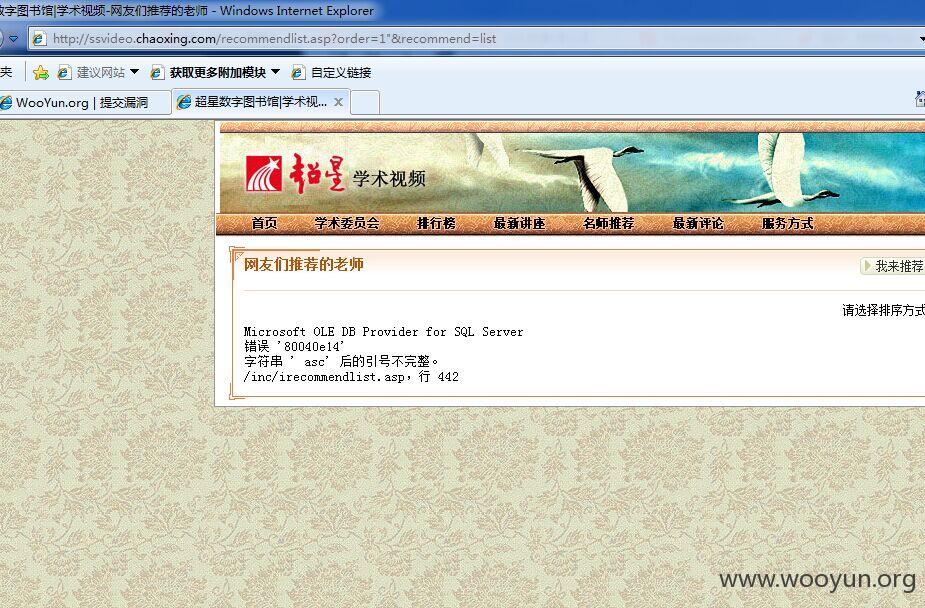
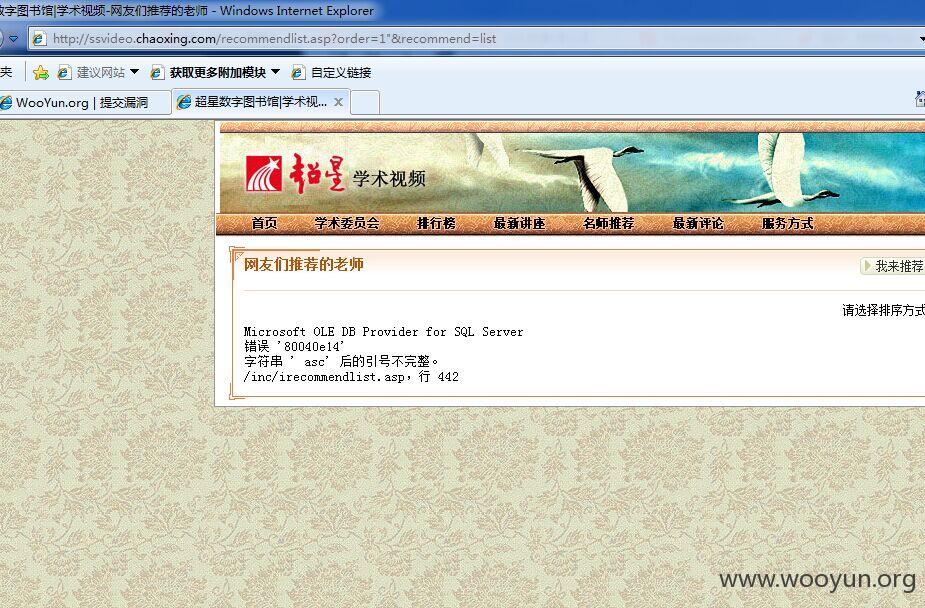
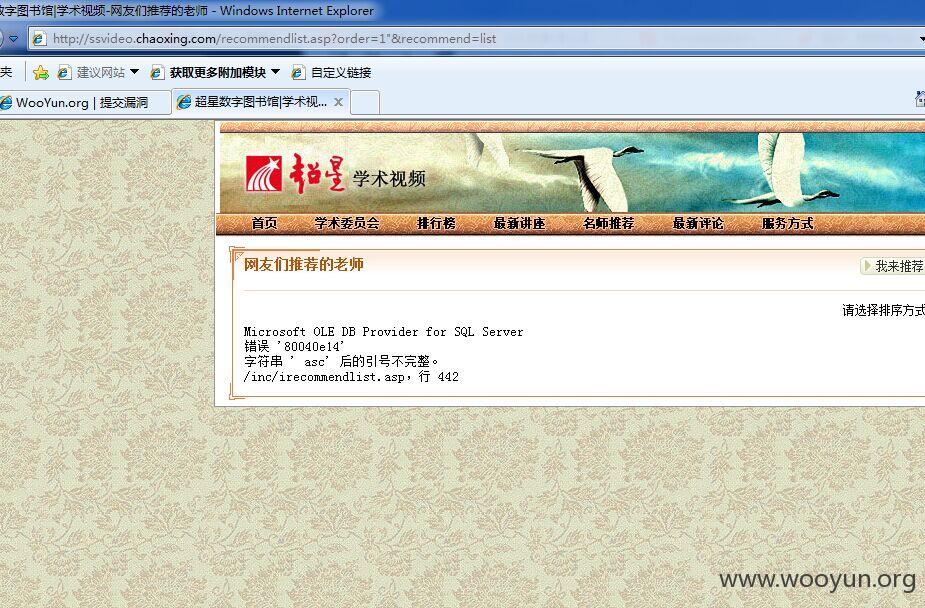
存在漏洞的页面recommendlist.asp
盲注什么的。。网太卡就不深入了。。这个洞审核的时候需要多测试几遍,有时候sqlmap注入会超时。。
如果检测的时候出错可以手工证明一下
漏洞网站:ssvideo.chaoxing.com
网站需要登录才能访问,手工猜出来一个test/test
登录之后即可访问网站。
存在漏洞的页面recommendlist.asp
盲注什么的。。网太卡就不深入了。。这个洞审核的时候需要多测试几遍,有时候sqlmap注入会超时。。
如果检测的时候出错可以手工证明一下